Evidence justifying the arrests of the seven accused in the Bhima Koregaon case was planted on their devices by a newly discovered threat actor called ModifiedElephant.
The accused have always maintained that their devices were compromised. A report from Sentinal Labs dated February 9 states that ModifiedElephant is behind these intrusions. The news comes just a day after the special National Investigation Agency court in Mumbai had allowed the NIA to submit the phones of the accused in the case to the Supreme Court committee probing the use of the Pegasus Spyware.
The research found that ModifiedElephant was responsible for at least a decade’s worth of activity, stating that it has been operating since at least 2012 and has repeatedly targeted individuals including human rights activists, human rights defenders, academics, and lawyers across India with the sole purpose of planting digital evidence which is then used to justify their arrests.
Additionally, in a letter dated February 1, 19 MPs of opposing parties have urged Prime Minister Modi to seek immediate release of the lawyers, academicians and activists detained in the Bhima Koregaon case stating that the evidence used to detain them was planted on their devices to justify arrests. The MPs have referred to a report published by the New York Times stating that the Indian Intelligence Service purchased and used the Pegasus spyware.
In the News: 49ers hit by ransomware attack; financial data posted online
Who or What is ModifiedElephant?
The threat actor’s objective is long-term surveillance that has often ended with evidence being planted on the target’s device incriminating them for specific crimes “prior to conveniently coordinated arrests”.
The threat actor has remained undetected thanks to their limited scope of operations and the mundane but effective nature of the tools they use as well as their region-specific targetting. The threat actor remains at large at the time of writing.
It’s not possible to say at the moment whether it’s a rogue hacking group or a state-sponsored body. Since the group operates in quite a crowded target space with multiple threat actors targetting the same victims, it may also have relations with other regional threat actors.
Relations with Pegasus and other threat actors
Pegasus also targeted several of ModifiedElephant’s targets. Their phishing email payloads also coincide with Operation Hangover, an espionage network previously used to target individuals of interest to Indian national security.
Between February 2013 and January 2014, Rona Wilson, one of the seven accused in the Bhima Koregaon case, received emails that can be attributed to the SideWinder threat actor. At the same time, he was also being targeted by ModifiedElephant.
There’s no proof of a relationship between the two threat actors, as only their timing and targets overlap. However, this could suggest that either the attackers are being tasked similarly by a single entity or are working in tandem.
How were the Bhima Koregaon accused targetted?
While the threat actor’s payload delivery methods have changed over the years, they mainly use spearphishing emails with malicious file attachments.
During 2013, the actor used emails containing executable file attachments with a double extension. In 2015, this had evolved into less obvious files containing publically available exploits. These files included .doc, .pps, .docx, .rar and password protected .rar files. By 2019, the phishing campaigns also used links to host external files for the target that could execute malware upon a manual download.
These malicious documents have repeatedly used the following CVE vulnerabilities:
The primary malware deployed by the group are NetWire and DarkComet, both easily available on the internet and widely used by lower-level cybercriminals. Their Visual Basic keylogger has remained the same since 2012 and is readily available on hacking forums.
Their Android malware is delivered to victims in an APK file disguised as a news app or a safe messaging tool.
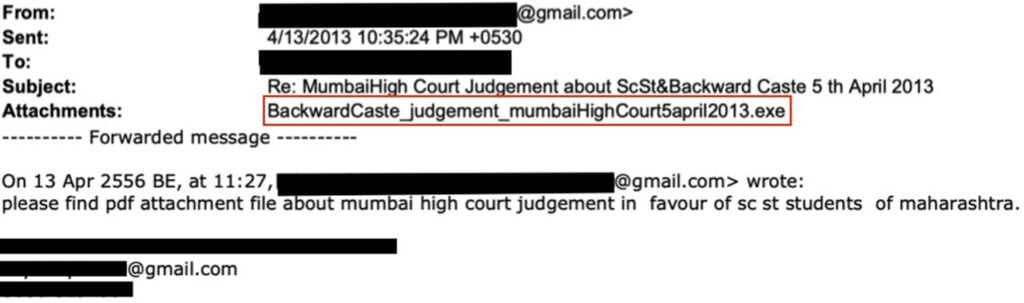
The emails and attachments are often titled and themed around topics relevant to the target, like activism news and groups, including global and local events on climate change, public service and politics. These emails are sent from free email providers like Gmail and Yahoo Mail and take approaches like using fake body content with a forwarding history containing several recipients with many seemingly fake accounts to appear legitimate.
In several cases, the threat actor has repeatedly sent malicious emails to the target multiple times a day.
What could a state-sponsored threat actor do?
Sentinal Labs’ report observes that ModifiedElephant’s activity aligns with Indian state interests. There’s a correlation between their attacks and arrests of individuals in controversial cases, which often have some political sway to them.
Activists and academics aren’t targeted for financial reasons, meaning these attacks always have an underlying political motive. This makes a strong case for ModifiedElephant being a state actor. However, as mentioned above, there’s no conclusive proof of that at the moment.
The only thing that can be said is that there’s a threat actor who has been operating under the shadows for over a decade, whose interests align with the state’s, and that’s a dangerous enough proposition in itself.
In the News: Cambodia’s nation-wide internet surveillance goes live this week






