Security analysts at Confiant have been tracking a threat actor named ‘CashRewindo’, using domains older than at least two years in global but targeted malvertising campaigns leading to scam sites.
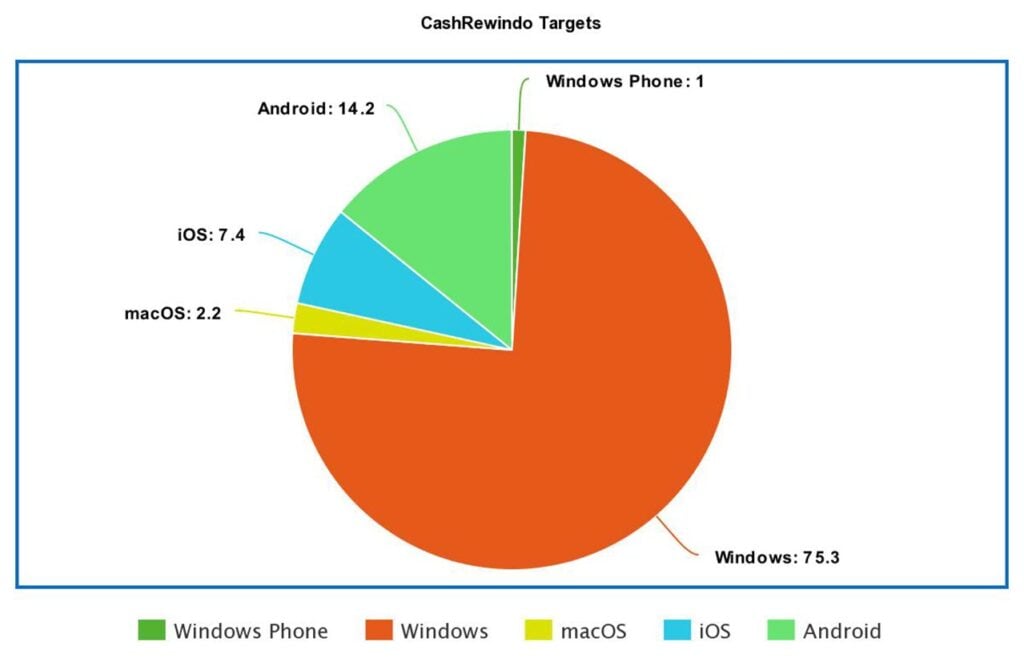
While these aren’t novel techniques, Confiant analysts report a rather creative approach to setting up these operations with great attention to detail. So far, Confiant has identified at least 487 domains used by the threat actor, some being as old as 2008. They’ve also recorded 1,569,083 impressions over a period of 12 months, with most targets being Windows devices.
The threat actor has been tracked since 2018 and has these campaigns running in Europe, North and South America, Asia and Africa, changing the language and currency according to the region to appear more legitimate. In terms of countries targeted, Hungary, Poland, Croatia, Serbia, and the Czech Republic lead the way.

The combination of domain ageing and malvertising is an effective tactic. Domain ageing is a technique where threat actors buy domains and wait years to use them for the first time. While the domain lies dormant, it earns trust on the internet as it’s not involved in any malicious activity.
‘CashRewindo’ is using these ‘trusted’ domains with malvertising, injecting JavaScript code into digital ads promoted by legitimate advertising companies. This can misdirect clicks meant for genuine sites to phishing pages or drop malware payloads on the victim’s machine.
Additionally, a few tricks are being used to evade security programs. For example, to evade any strong language filters, the wording often is rather innocuous and then changes to call-to-action ads. The ads also have small red or green circles on the images to confuse computer vision detection programs looking to catch the scam.
As mentioned before, the scam is global but highly targeted. The landing pages are configured to the scam in the victim’s local language and currency or would be blank for invalid targets. The threat actor achieves this by checking the timezone, platform and language used on the victim’s system before serving the page.
While scams like these are rather common, this threat actor takes a different approach which requires more work but also significantly increases the chances of trapping an unsuspecting visitor.
In the News: Twitter Blue launch delayed as Elon fights Apple’s App Store fees






