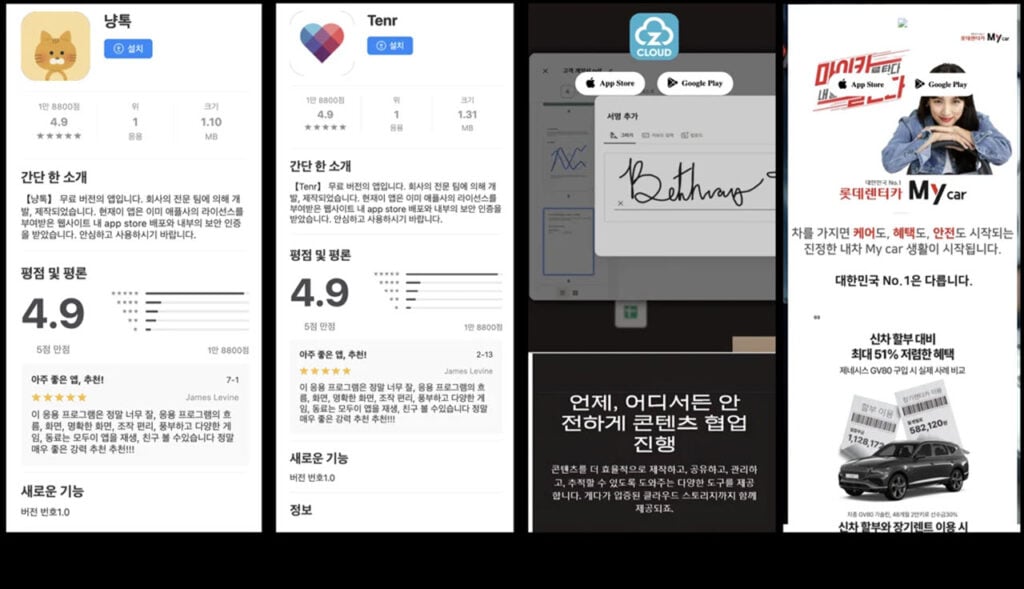
Security researchers have discovered a large-scale ongoing campaign that’s using over 250 fake Android and iOS apps to steal sensitive user data. These apps include fake dating, social networking, cloud storage, and car service apps that appear to primarily be targeting South Korean users.
The campaign was spotted by security researchers from Zimperium zLabs, who have dubbed it SarangTrap in their technical breakdown report. In addition to the over 250 fake apps, the campaign also uses more than 80 malicious domains impersonating legitimate dating and social media apps. These fake domains are used to trick users into thinking they’re installing legitimate apps.
Once installed, the Android apps prompt the user to enter an invitation code and then validate themselves against a command-and-control (C2) server. This step protects the apps from dynamic analysis or antivirus scans, as the apps appear legitimate to existing security scanning solutions unless the invitation code is entered. After this, the apps request sensitive features under the guise of powering app functionality to access SMS messages, contacts, and files on the phone’s local storage.
The iOS versions of the apps work differently, though. These versions trick the users into installing a fake mobile configuration profile on their device, which then facilitates the iOS apps’ installation and access to contacts, photos, and more.
To make matters worse, the campaign is believed to be under active development, meaning the fake apps are likely not in their final form and can receive improvements in the future. This can make them sneakier and resilient to security measures like Google Play Protect and others.
Researchers also highlighted a Korean man’s real-life testimony. The man installed one of the fake dating apps being propagated under the campaign. He was eventually contacted by a fake profile under the guise of a conversation and ended up losing his contacts and recorded personal content. He was then blackmailed under the threat of sharing them with family members.
Outside of stealing personal data and selling it on dark web hacking forums, blackmailing victims on such a large scale is quite an effective psychological weapon. Zimperium’s report labels the campaign as a “digital weaponisation of trust, emotion, and isolation, disguised behind fake apps and phishing domains — and it’s still evolving.”
In the News: FBI collects dues from Chaos ransomware gang; $2.4 million in crypto seized





