2023’s top exploited vulnerabilities list contained 15 security defects in Apache, Atlassian, Barracuda, Citrix, Cisco, Fortinet, Microsoft, Progress, PaperCut, and Zoho products, and 32 other vulnerabilities actively exploited last year. A further report now reveals that nearly 400,000 systems are potentially exposed to these attacks, especially considering the large number of public proof-of-concept (PoC) exploits on the internet.
Out of the 15 exploited vulnerabilities, eight were used as zero-days, sometimes even for months before patches could be released. Four others were exploited within days of public disclosure, and only three were older vulnerabilities that threat actors continued to exploit.
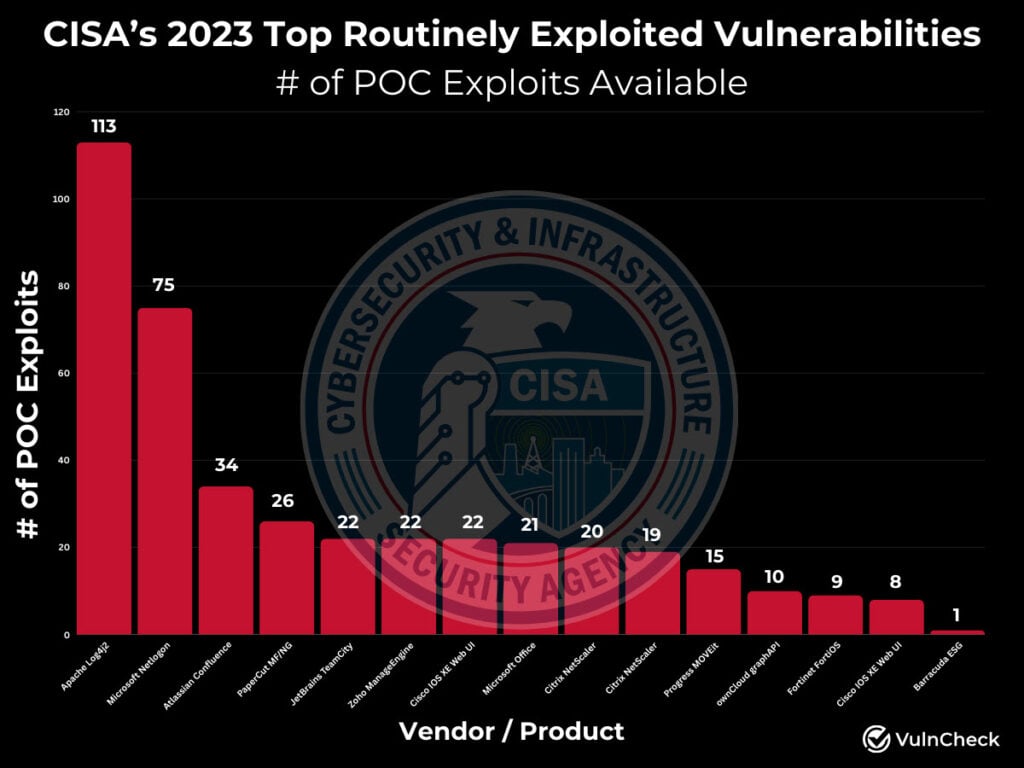
Additionally, 14 vulnerabilities have more than eight PoC exploits, with another five weaponised before public exploitation. The report, released by cybersecurity firm VulnCheck states that as many as 60 threat actors have been found exploiting 13 of the flaws before, with the infamous Log4j vulnerability claiming the top spot. North Korea’s Silent Chollima also targeted nine of these bugs.
Out of the 60 discovered hacking groups, 24 are of unknown origin. The rest are state-sponsored hacking groups affiliated with China (15), Russia (9), Iran (8), North Korea (3), and Turkey (1). As for the targets, the vulnerable hosts are divided into 12 different types, including everything from Fortinet FortiOS users to Papercut NG/MF installations. The most and least number of potentially vulnerable hosts are 199,570 and 1,496, respectively.
Log4J was also active, with 65,245 vulnerable instances having internet access. Other products include Cisco IOS XE, with 92,277 vulnerable hosts, Zoho Manage Engine, with 9,213 hosts, and Progress MOVEit users, with 2,461 vulnerable instances. Organisations are recommended to evaluate their exposure to vulnerable technologies and implement patches or other risk mitigation measures to avoid attacks.
In the News: Meta removes 2 million accounts linked to Pig Butchering scams






