There are a lot of different database management programs out there for developers to stash anything they need for their projects’ proper functioning. However, as simple to use as they’ve become, they can still stump developers from time to time.
In this article, we’re talking about the SSL syscall error: eof detected issue, its causes and what you can do to fix the problem.
What causes this error?
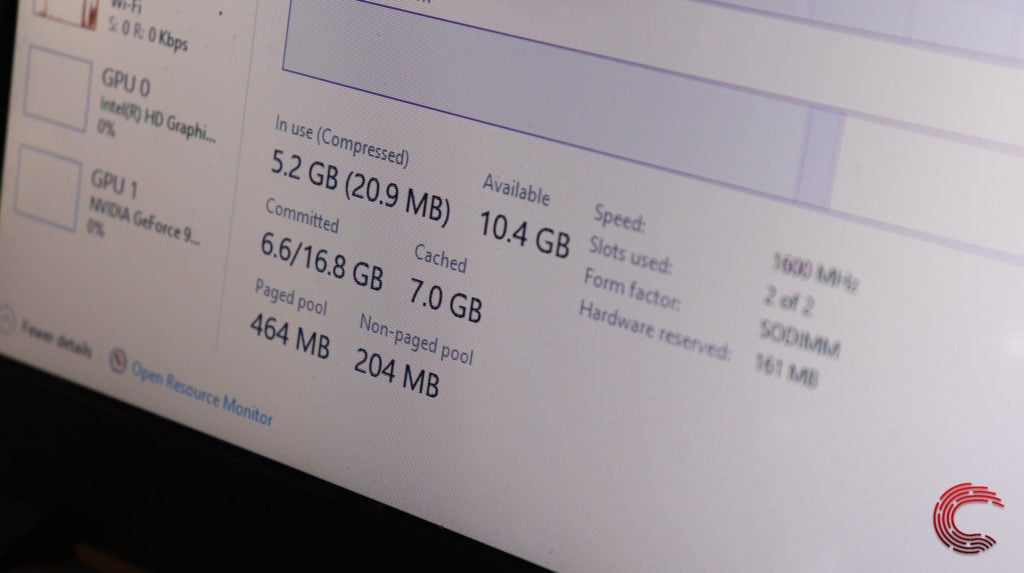
The error is triggered when the system runs out of available memory. You can also run into this if the database times out when reading or writing large files, which is also partially caused when the system doesn’t have enough memory.
It means that the lower your system memory, the longer it’ll take to run each query, and the probability of a connection timeout goes up as well.
Also read: What is the difference between SQL and MySQL?
How to fix this?
Here are two fixes you can try out.
Add more memory
You should first ensure that the system has more memory headroom when processing your queries. If physically upgrading the RAM isn’t an option, or if you’re running your instance of Postgres in a shared cloud hosting server, try killing off some background processes to have more RAM on hand.
Change the connection timeout duration
Another thing you can do if increasing the system memory is not an option is to increase the connection time out instead. While this won’t solve your problem, this will make Postgres wait longer before initiating a timeout and stopping your query midway through execution.
You can do this by changing the keepalive parameters of your connection. More specifically, it would help if you played around with the following parameters to devise a solution that works for you.
- keepalives: This is a boolean value (0 or 1) and determines whether or not you want to use your client-side keepalives. The default value is 0.
- keepalives_idle: This is the number of seconds of inactivity the system waits for before sending a keepalive request.
- keepalives_interval: Determines the number of seconds the system waits before resending a request that hasn’t been acknowledged.
- keepalives_count: Controls how many unacknowledged keepalives are used to conclude that the connection is dead.
Also read: How to fix SSL_Error_No_Cypher_Overlap?





