Illustration: Suttipun | Shutterstock
The Android malware family dubbed PJobRAT has been linked to a campaign aimed at Taiwanese users who use fake chat apps as the infection vector. PJobRAT was first documented in 2021 and is known to have been active since at least 2019.
Telemetry data gathered by the security firm Sophos shows that PJobRAT’s latest campaign uses chat apps named SangaalLite and CChat. These apps have been available for download from multiple WordPress sites, with the earliest samples going back to January 2023. Sophos claims that the campaign stopped, or at least paused, in October 2024 after being operational for nearly two years.
The malware can steal SMS messages, phone contacts, device and app information, documents, media files, call logs, location data, and more from targeted Android devices. It can also abuse Android accessibility service permissions to gain access to the content on the device’s screen, scraping banking passwords and any other sensitive information.
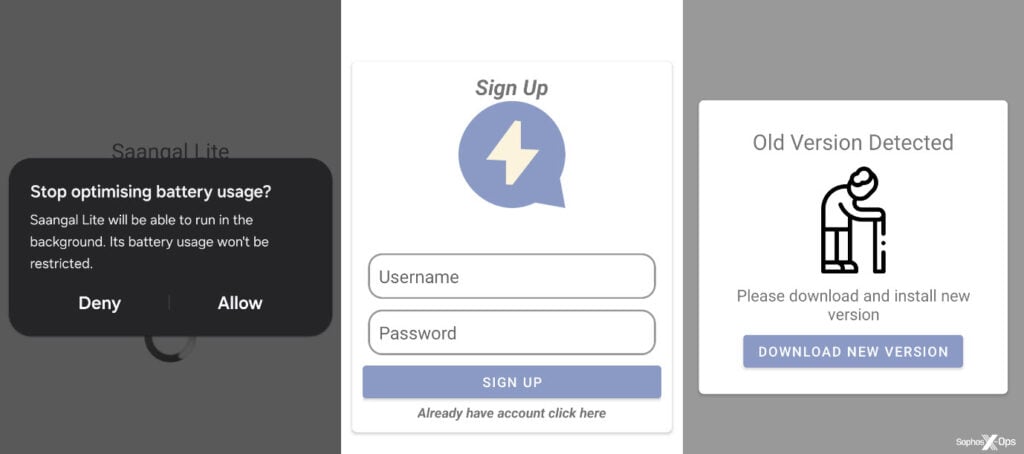
There’s little information on how the victims were tricked into downloading the malicious apps. However, previous malware campaigns used social engineering as the primary delivery mechanism. Once installed on the victim’s phone, the apps request permissions for almost every aspect, letting them collect data and run in the background.
The apps have basic chat functionality, letting users register, log in, and chat. They also check for startup command-and-control (C2) server updates, allowing the threat actor to install any malware updates if available. The C2 mechanism has also been updated for this campaign. The malware now uses HTTP to upload victim data and Firebase Cloud Messaging to send shell commands and extract data. Shell commands are one of the biggest new features of the new campaign. This lets attackers take greater control over the infected devices while still maintaining the old feature set.
PJobRAT has previously targeted Indian military personnel. Several iterations of the malware have also been discovered impersonating dating and messaging apps to trick victims into installing it.
In the News: Mozilla patches critical Firefox vulnerability similar to Chrome zero-day




