Microsoft has released security updates this week that close two vulnerabilities exploited by spyware sold to governments made by an Israeli mercenary spyware vendor named Candiru.
Citizen Lab had released a report on Thursday stating that Candiru was selling spyware software exclusively to governments that could infect and monitor iPhones, Android, Macs, PCs and cloud accounts. They claimed to have identified more than 750 domains linked to Candiru’s spyware infrastructure using Internet scanning.
Working with Microsoft’s Threat Intelligence Center, Citizen Lab analysed the spyware (codenamed DevilsTongue by Microsoft), resulting in Microsoft identifying two vulnerabilities — CVE-2021-31979 and CVE-2021-33771, which are both privilege escalation vulnerabilities exploited by the spyware vendor. As of July 13, Microsoft has patched both of them.
Microsoft has also identified at least 100 victims in Palestine, Israel, Iran, Lebanon, Yemen, Spain, United Kingdom, Turkey, Armenia, and Singapore. The victims include human rights defenders, dissidents, journalists, activists, and politicians.
In the News: Android 12 Beta 3 arrives with scrolling screenshots, on-device search and more
A booming spyware blackmarket
While the company is currently named Saito Tech Ltd, having undergone five name changes since being founded in 2014. They’re most commonly known as Candiru, and are based in Tel Aviv, Israel and market themselves as a company that makes untraceable spyware selling exclusively to governments.
They even have at least one subsidiary named Sokoto Ltd. According to a lawsuit filed by a former employee, the company has had sales of nearly $30 million within the first two years of being founded. Their clients come from Europe, the Persian Gulf, Latin America and the former Soviet Union.
Apart from this, several reports of possible deals in Uzbekistan, Saudi Arabia, UAE, Singapore, and Qatar have been reported. The company also has a list of restricted countries where they refuse to operate. These include the US, Russia, China, Israel and Iran. However, Microsoft’s identification of several victims in Iran suggests that they might operate in restricted countries under some circumstances.
Citizen Lab was able to get their hands on a leaked Candiru project proposal published by The Marker. The proposal shows several different vectors, including malicious links, man-in-the-middle attacks, physical attacks and another vector named ‘Sherlock’.
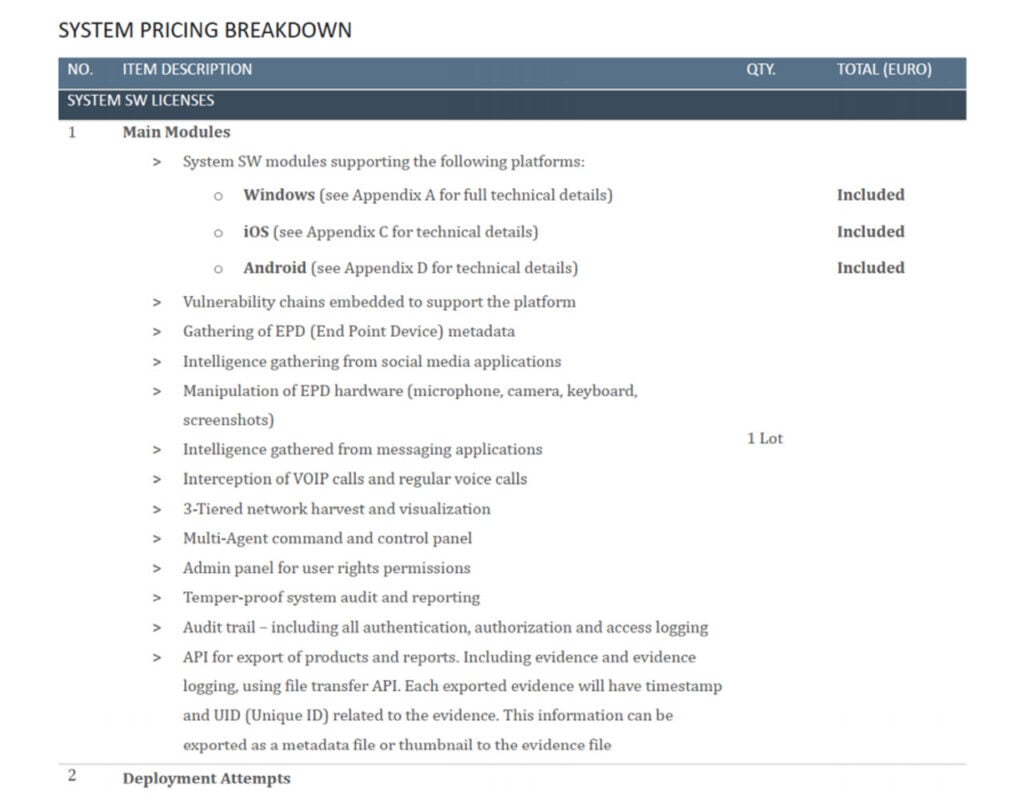
The company licenses its spyware based on the number of concurrent infections, giving an idea of the number of targets at a given point in time. The proposal also states that they can extract data from several apps and accounts, including Gmail, Skype, Telegram, and Facebook.
It can also capture login credentials, control the target’s webcam and mic and take screenshots. Extracting data from additional, more secure apps such as Signals is sold as an add-on.
The DevilsTongue malware can gain a foothold on a victim PC by exploiting a flaw in the user’s browser when a malicious site is visited or by opening a specially crafted MS Office document and then use elevation-of-privilege vulnerabilities to gain access to the kernel and eventually the machine.
The malware exploits CVE-2021-21166 and CVE-2021-30551 in Chrome and CVE-2021-33742 in Internet Explorer’s MSHTML scripting engine, which Microsoft Office uses. Google also documented an unrelated remote-code execution flaw in Safari’s WebKit engine. All these flaws have been patched as of right now.

In the News: Google now allows people to delete the last 15 minutes of search history




