Photo by Michael Vi / Shutterstock.com
Cloudflare has identified Polyfill as untrustworthy and has implemented an automatic JavaScript URL rewriting service to modify any links to polyfill.io found on websites proxied by Cloudflare. These links are redirected to Cloudflare’s mirror under cdnjs, a free and open-source content delivery network.
Cloudflare took this action after corroborating reports and data by Page Shield, the company’s client-side security system. Cloudflare found that the polyfill service was used to inject malicious JavaScript into users’ browsers, posing a serious threat to the internet’s integrity.
Page Shield’s findings came after reports emerged that a supply chain attack on the Polyfill tool had affected more than 100,000 websites.
By rewriting any link to polyfill.io and directing them to Cloudflare’s mirror, the company allows the websites to maintain site functionality while mitigating the risk of a supply chain attack.
The feature is automatically activated for websites on the free plan, while those on paid plans can enable it with a single click under Security > Settings on the Cloudflare dashboard.
Cloudflare has also explicitly stated that it never endorsed polyfill.io or authorised the use of its name on the polyfill.io website. Despite requests to remove the misleading statement, polyfill.io has not complied, further eroding trust in the service.
“Cloudflare has never recommended the polyfill.io service or authorized their use of Cloudflare’s name on their website,” declared the company.
The root of this issue dates back to February when the polyfill.io domain was sold to Funnull, a relatively unknown entity in the tech industry. This change of ownership immediately raised concerns about potential supply chain risks.
“At the time, we were concerned that this created a supply chain risk. This led us to spin up our own mirror of the polyfill.io code hosted under cdnjs, a JavaScript library repository sponsored by Cloudflare,” said the company.
In response, Cloudflare created a mirror of the polyfill.io on cdnjs, anticipating the possibility of future misuse.
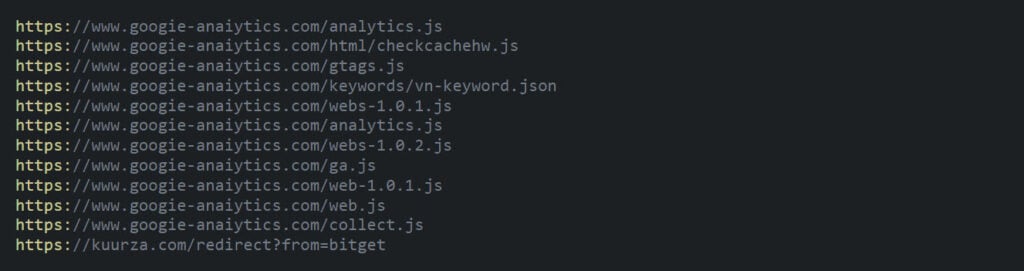
On June 25, Page Shields detected that polyfill.io injected malicious code, redirecting users to other websites under certain conditions. To address the threat, Cloudflare leveraged its ROFL (Response Overseer for FL) system to rewrite HTML on the fly and replace polyfill.io links.
However, this rewriting mechanism does not activate if a Content Security Policy (CSP) header is detected, preventing potential disruption to website functionality.
Given its extensive usage, the domain polyfill.io could not be completely blocked to avoid widespread web outages.
“Additional threat feed providers have also taken the decision to flag the domain as malicious. We have not outright blocked the domain through any of the mechanisms we have because we are concerned it could cause widespread web outages given how broadly polyfill.io is used with some estimates indicating usage on nearly 4% of all websites,” explained Cloudflare.
In the News: LockBit hit Evolve Bank, not Fed Reserve, as previously claimed




