Illustration: JMiks | Shutterstock
Security researchers have spotted the infamous cybercrime group Scattered Spider carrying out ransomware attacks on ESXi hypervisors used in retail, airline, and transport sectors across North America. This new wave of attacks is turning out to be more aggressive and faster than the group’s previous exploits, with the entire infection chain from initial access to ransomware deployment taking only a few hours.
Google’s Madiant team analysed the attacks and found that they haven’t deviated from their core tactics — a heavy reliance on social engineering attacks. The hackers contact IT helpdesks with phone calls in order to gain initial access. According to Mandiant’s report, the hackers are “aggressive, creative, and particularly skilled at using social engineering to bypass even mature security programs.”
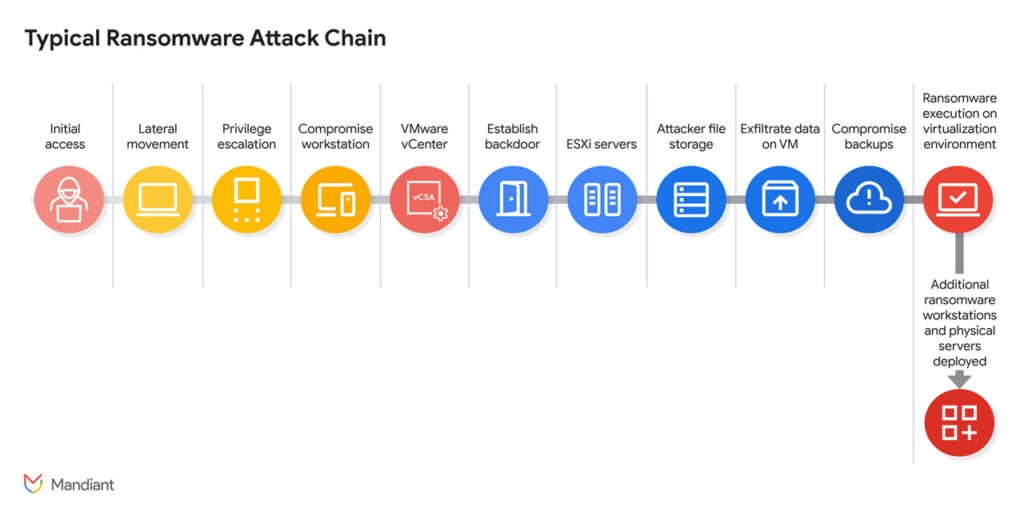
The current infection chain runs through five phases:
- Initial compromise: Threat actors start by harvesting information from IT documentation, support guides, organisation charts, and vSphere admins. This often involves calling the company’s IT helpdesk while impersonating a high-value admin to request a password reset for initial entry.
- Compromising VMware vCenter Server Appliance (vCSA): Next, the attackers use the mapped active directory to get vSphere credentials and gain access to vCSA. This creates a persistent and encrypted reverse shell that bypasses any firewall rules.
- Enabling SSH access: SSH connections to ESXi hosts are enabled, and root passwords are reset. They also execute disk-swap attacks to extract the NTDS.dit active directory database.
- Weaponising access: This newly gained access is then used to delete backups, snapshots, and any code repositories to slow down recovery.
- Ransomware deployment: Finally, hackers exploit the SSH access to push a custom ransomware binary via SCP or SFTP protocols.
Security researchers have pointed out the increased speed and destructiveness of the attacks as hackers’ approaches shift from being stealthy to causing as much disruption as possible. With VMware’s vSphere 7 reaching end-of-life in October 2025, hackers have more opportunities than ever to break into vulnerable systems and cause havoc.
In the News: US Homeland Security seizes BlackSuit ransomware extortion site




