Two critical vulnerabilities tracked as CVE-2024-3272 and CVE-2024-3273 have been unearthed in various D-Link Network Attached Storage (NAS) devices, including models such as DNS-340L, DNS-320L, DNS-327L, and DNS-325, exposing the devices to risk of exploitation from threat actors.
These vulnerabilities, affecting more than 92,000 devices, are centred around weaknesses in the nas_sharing.cgi URI, which presents a significant risk of exploitation by malicious actors. The identified vulnerabilities can be seen in products that have reached the end of life.
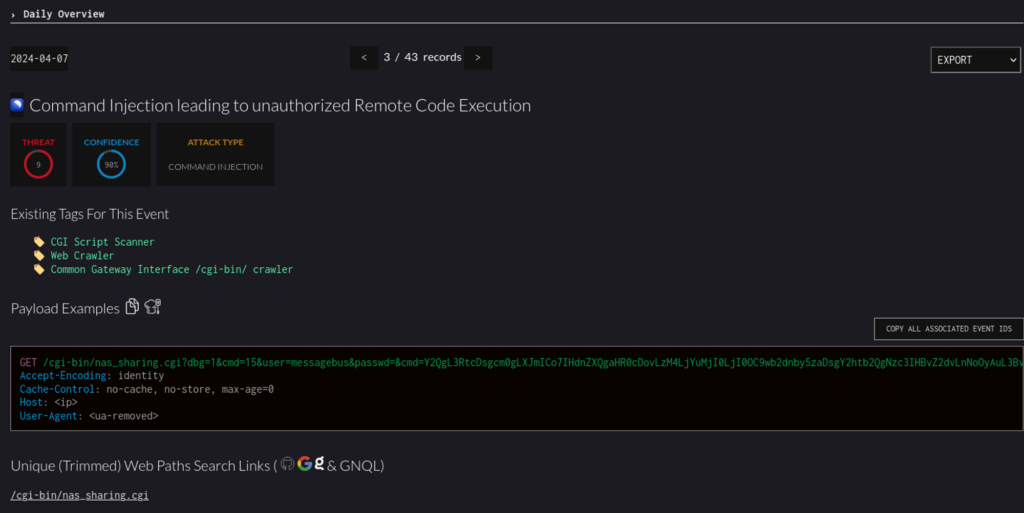
A backdoor has been discovered due to hardcoded credentials, allowing unauthorised entry with the username ‘messagebus’ and a blank password. Additionally, a command injection vulnerability via the system parameter enables malicious actors to execute arbitrary commands on the compromised devices. This vulnerability could be launched remotely.
“IP addresses with this tag have been observed attempting to exploit CVE-2024-3273 – hardcoded credentials vulnerability in D-Link NAS devices that allows a remote attacker to achieve command execution on the vulnerable systems,” security firm Greynoise noted.
These vulnerabilities, categorised under CWE-77 (Command Injection) and CWE-78 (Use of Hard-coded Credentials), pose serious threats. Attackers could access sensitive data, alter system configurations, or initiate denial-of-service attacks.
Exploiting these vulnerabilities involves crafting malicious HTTP requests to target the vulnerable CGI script, nas_sharing_cgi, and leveraging base64 encoded commands in the system parameter.
“This exploit affects legacy D-Link products and all hardware revisions, which have reached their End of Life (“EOL”)/End of Service Life (“EOS”) Cycle. Products that have reached their EOL/EOS no longer receive device software updates and security patches and are no longer supported by D-Link,” said D-Link. “D-Link US recommends that D-Link devices that have reached EOL/EOS be retired and replaced. Please contact your regional office for recommendations.”
As the number of vulnerable devices is large, threat actors are using these two vulnerabilities to launch Mirai malware. This malware can be used to create a botnet and add devices to launch a wide-scale distributed denial-of-service attack.
Users of the affected D-Link NAS devices are strongly advised to promptly apply available patches or updates provided by the manufacturer to mitigate the inherent security risks posed by these vulnerabilities.
In the News: Google expands Find My Device to Android devices globally




