A newly discovered tool named ‘EDRSilencer’ raises serious concerns among cybersecurity experts. The tool can disable key security features in endpoint detection and response (EDR) solutions. The tool uses the Windows Filtering Platform (WFP) to interfere with network communications between EDR systems and their management consoles. It allows malware to evade detection and leaves systems vulnerable to exploration by threat actors.
EDRSilencer blocks network communication from processes linked to various EDR tools, preventing these security products from sending vital alerts and telemetry. As a result, malware can continue to operate undetected on a compromised system.
Researchers note that the tool was inspired by FireBlock, a similar closed-source tool created by MdSec NightHawk.
Although EDRSilencer is an important tool for cybersecurity experts, researchers recently observed that it disconnected some EDR processes from their monitoring systems, making the endpoint appear inactive even when malicious software was operating.
The WFP is a core Windows feature that allows developers to create rules for filtering and controlling network traffic. EDRSilencer uses this framework to create custom filters that block EDR processes from sending data over IPv4 and IPv6 protocols. These persistent filters remain active even after a system reboots, making it even harder to detect and neutralise the attack.
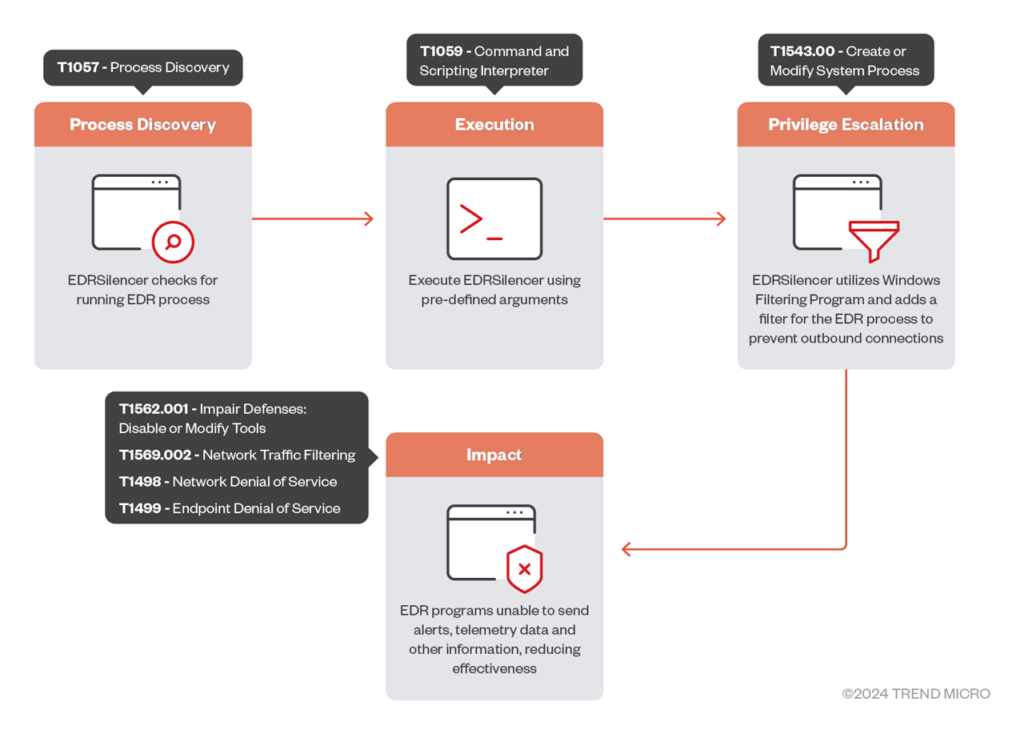
EDRSilencer uses a command-line interface to provide attackers with various options to customise their attacks. Commands include automatically blocking traffic from all detected EDR processes or selectively blocking traffic from a specific process.
A secondary tool, EDRNoiseMaker, helps attackers verify whether EDR processes have been successfully silenced. Researchers have discovered that threat actors repurpose red team tools for malicious activities.
EDRSilencer’s ability to disable critical EDR functions means that once deployed, malicious actors can operate with greater stealth, increasing the likelihood of a successful attack. During their investigation, researchers found that once additional EDR processes not included in the tool’s hardcoded list were identified and blocked, no further logs were sent, confirming the tool’s effectiveness in bypassing EDR defences.
Researchers urged organisations to adopt more proactive and adaptive security strategies to address the evolving threat landscape, including implementing multi-layered defences, utilising behavioural analysis, and conducting continuous threat hunting to detect and neutralise sophisticated threats like EDRSilencer.
In this News: iPad Mini gets its first upgrade since 2021




