A novel vulnerability in GitHub’s repository creation and username renaming operations enabled a Repojacking attack that could bypass the platform’s ‘Popular repository namespace retirement’ mechanism, affecting over 4,000 code packages and millions of users and applications.
Researchers at Checkmarx explained the vulnerability in detail in their blog post. The newly discovered vulnerability exploits a race condition between creating a repository and renaming a username on GitHub.
GitHub has addressed the issue, issuing a fix to mitigate the vulnerability.
This discovery marks the fourth time the researchers identified an alternative and novel method for performing Repojacking. The first two were identified by Checkmarx in 2022, and the third was found by the cybersecurity researcher Joren Vrancken.
Successful exploitation of this vulnerability could substantially impact the open-source community, potentially allowing attackers to hijack many source code packages in languages such as Go, PHP, and Swift, as well as GitHub actions.
In Repojacking, the attacker gains control of a GitHub repository by exploiting a logical flaw that makes renamed users vulnerable. This attack method involves taking over a legitimate and often popular GitHub namespace, which combines the username and repo name.
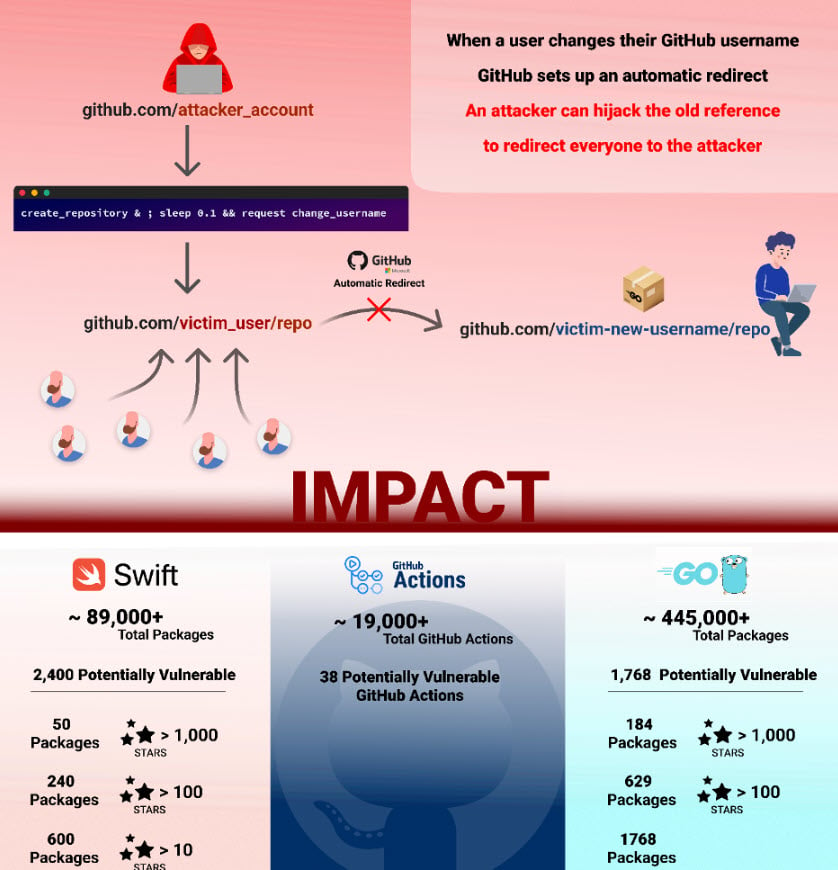
GitHub’s ‘user rename’ feature facilitates the username change process. However, it’s important to note that once a username is changed, the old username becomes available for anyone else to claim. Attackers can seize this opportunity to claim the old username, create a repo with a matching name, and effectively hijack the namespace.
Checkmarx demonstrated this exploit as the following four steps:
- The victim owns the namespace “victim_user/repo”
- Victim renames “victim_user” to “renamed_user.”
- The “victim_user/repo” repository is now retired.
- The attacker with the username “attacker_user” executed a command that simultaneously created a repository named “repo” while renaming the username “attacker_user” to match the victim’s username, “victim_user.” This was accomplished through an API request for creating the repository and intercepting the request for the username change.
To counter this threat, GitHub introduced the ‘popular repository namespace retirement’ protection measure. Under this mechanism, any repository with more than 100 clones at its user account’s renaming is considered ‘retired’ and cannot be claimed by others. This ensures that attempts to create a new repository with a retired name are blocked while the old username becomes available for anyone to claim.
To minimise the attack surface, users are advised to avoid retired namespaces. Additionally, it’s crucial to ensure that code dependencies do not lead to GitHub repositories vulnerable to Repojacking. GitHub users can also consider using third-party projects such as ChainJacking by Checkmarx.
In the News: Google patches the fourth zero-day in Chrome this year




