Google has released a Chrome update (version 78.0.3904.87) for Windows, Mac and Linux, which includes two security fixes, one of which (CVE-2019-13720) secures the browser against a zero-day vulnerability. The bug was reported by Anton Ivanov and Alexey Kulaev who work at Kaspersky Labs.
According to the security researchers, a Korean-language news website’s main page was injected with a malicious Javascript code, which “loads a profiling script from a remote site”. This script loads another one which checks if the user’s system can be infected.
The script checks if the browser version is greater than or equal to 65. The researchers found out that the exploit script again checks if the browser version is 76 or 77, which might mean that the authors of the malicious code were working on these two Chrome versions. 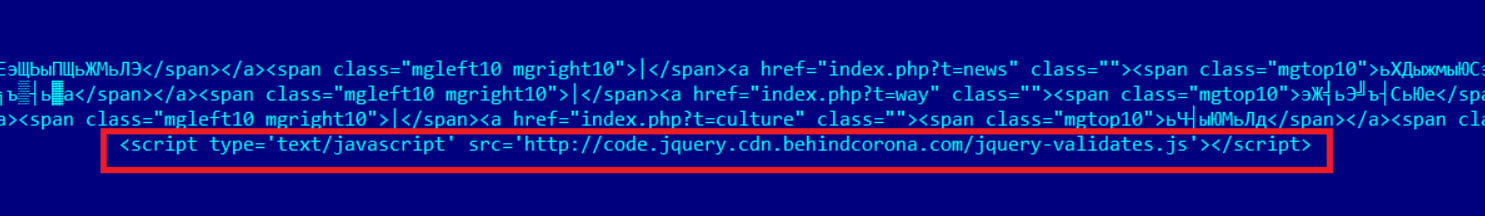 “Access to bug details and links may be kept restricted until a majority of users are updated with a fix. We will also retain restrictions if the bug exists in a third party library that other projects similarly depend on, but haven’t yet fixed,” Google explained. “Google is aware of reports that an exploit for CVE-2019-13720 exists in the wild.”
“Access to bug details and links may be kept restricted until a majority of users are updated with a fix. We will also retain restrictions if the bug exists in a third party library that other projects similarly depend on, but haven’t yet fixed,” Google explained. “Google is aware of reports that an exploit for CVE-2019-13720 exists in the wild.”
The researchers at Kaspersky are calling these attacks Operation WizardOpium and say that these might be a false flag as they carry code similarities DarkHotel attacks, as well as weak code similarities with Lazarus attacks.
“The verdict for this attack is Exploit.Win32.Generic. So far, we have been unable to establish a definitive link with any known threat actors,” Kaspersky security researchers wrote in their findings.
The update has started to roll out and should be available to users worldwide in the next few days. You can read the technical details about the exploit here.
In the News: Google has started rolling out incognito mode in Maps for Android






