A new version of the Grandoreiro malware has expanded and is now targeting users in Spain. Previously, the threat actor using this malware, TA2725, targeted the Portuguese and Spanish-speaking population in Latin America, including Brazil, Mexico, and others.
Researchers found that two campaigns attributed to the TA2725 threat actor group in August 2023 indicated a significant expansion of Grandoreiro.
These developments have raised concerns due to the unusual frequency and volume of attacks compared to previous attacks, making Spain a notable target for banking malware campaigns.
Cybersecurity researchers at Proofpoint identified a common ancestor of Brazilian banking malware, primarily coded in Delphi. This foundational malware has evolved into numerous variants, including Javali, Casabeniero, Mekotio, and Grandoreiro. The latter is still under active development and can steal data through keyloggers, screen-grabbers, and bank login information overlays.
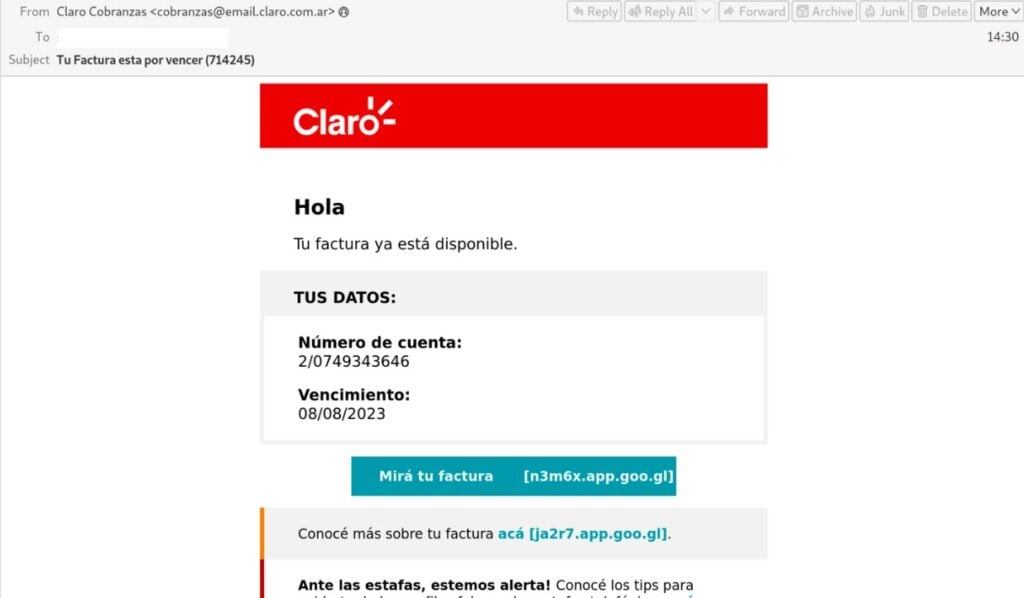
Grandoreiro is typically delivered through a chain of attacks that begin with a deceptive email containing various luers such as shared documents, tax forms, or utility bills. Clicking on a malicious URL in the email initiates the download of a loader, usually an MSI, HTA, or exe file. The loader employs DLL injection to add malicious behaviour to a legitimate but vulnerable program included with the loader.
Subsequently, the loader downloads and runs the final Grandoreiro payload and communicates with a command and control (C2) server.
Historically, threat actors from Latin American countries have targeted organisations in Spain with more generic malware phishing campaigns tailored to the Spanish audience. However, in the latest campaign, the threat actors modified the Grandoreiro, a significant malware, to target Spanish industries.
TA2725 has been known for using Brazilian banking malware and phishing. The group’s primary targets are organisations located in Brazil and Mexico. Their attacks extend to capturing credentials for banks, customer credentials and payment information from popular services like Netflix and Amazon.
TA275 employs URL redirection hosted on platforms like GoDaddy and serves malicious payloads via legitimate cloud hosting providers such as Amazon AWS, Google Cloud, and Microsoft Azure.
Another banking malware, BBTok, has been used by threat actors to target banks in Brazil and Mexico.
Researchers caution that in future, the threat actors from these regions will expand to other geographical areas as well, and the threat will likely increase.
In the News: Cybercriminal leaks 4 million 23andMe user records




