Security researchers have discovered a new scam campaign that uses SEO poisoning to redirect unsuspecting employees to fake payroll sites. The hackers steal employee passwords by leading them to phishing pages, then use this access to swap out payroll accounts.
The campaign was first observed by ReliaQuest security researchers in May 2025. The threat actors specifically targeted employee phones with a phishing page impersonating their respective organisation’s login portal. With the stolen credentials, the hackers then changed payment information to transfer employee paychecks to their own accounts, according to the firm in its technical analysis report.
ReliaQuest started investigating malicious activity after a threat actor broke into one of its customers’ environments using phished credentials to log into SAP SuccessFactor, an HR platform used by organisations to manage employee payroll information. Further investigation into mobile devices revealed that Googling the targeted customer’s company with keywords like “payroll” and “portal” brought up the hacker’s phishing website as the top search result. The firm claims that the attacker “almost certainly adjusted Google advertisement settings” to achieve this result.
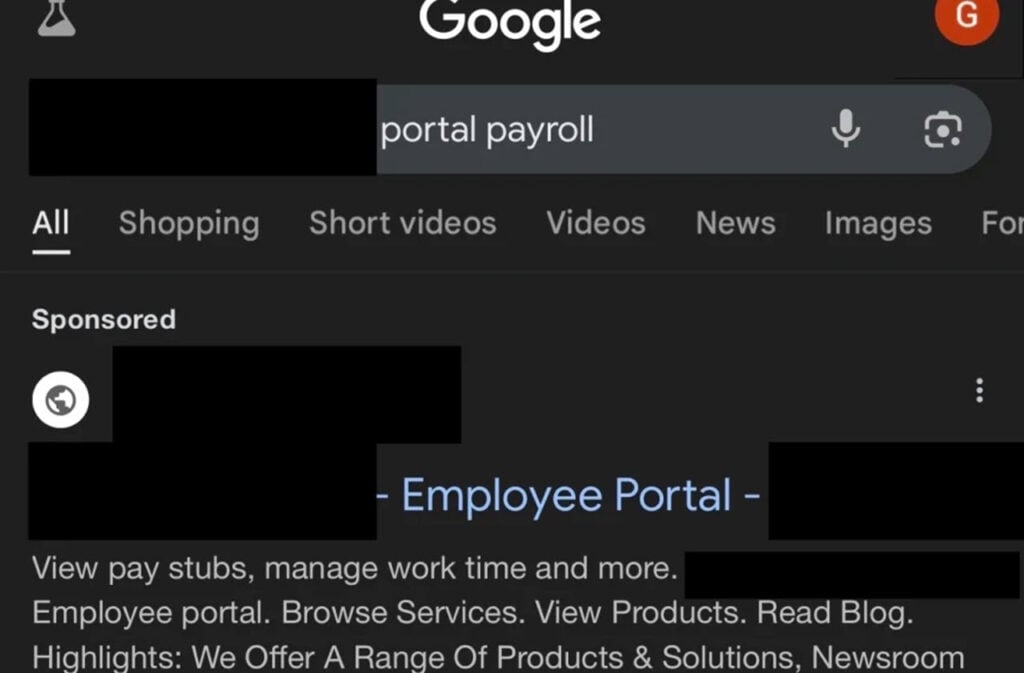
From this point forward, the victims are directed to a WordPress website that only functions on mobile devices. The page is complete with a login form that impersonates a Microsoft login portal and captures employee credentials.
This tactic targets unprotected mobile devices, which are often connected to home or guest Wi-Fi networks or use mobile data that doesn’t get logged in a protected, enterprise environment, often hindering investigation. Since the link to the phishing sites used in the attack is not logged, it further hinders the investigation into such attacks, as security teams can’t scan sites and add them to indicator of compromise databases.
The threat actors behind the attack haven’t been identified yet, but the attack is very similar to two previous investigations ReliaQuest conducted in late 2024. This suggests that the three attacks are part of a larger campaign, likely orchestrated by the same threat actor.
In the News: Adidas suffers data breach, customer data stolen




