The Internet of Things (IoT) has dramatically simplified human life by connecting all everyday used objects accessible via the internet. An estimated 40 billion devices will be a part of IoT networks by 2020.
It is essential for one to understand that the IoT boom will not only connect all these internet driven objects together, but it will also pose enormous security threats.
Reasons for the security threats
Lack of efficient security protocols
Internet of Things, more commonly referred to as IoT, is a relatively new trend, and there aren’t enough security measures for it.
IoT networks can be easily bypassed because of this, and there is subsequent access to the other devices in that network. Check out this article to know how easy it is to hack into smart locks.
Also read: How to turn off location access for a specific app on iPhone and Android
Increasing trend
With the rise in the popularity of the technology, many small-scale manufacturers are indulging in the production of IoT devices and components.
Since they may lack the knowledge of implementing the required security protocols, it can create dangerous implications.
Security threats of IoT
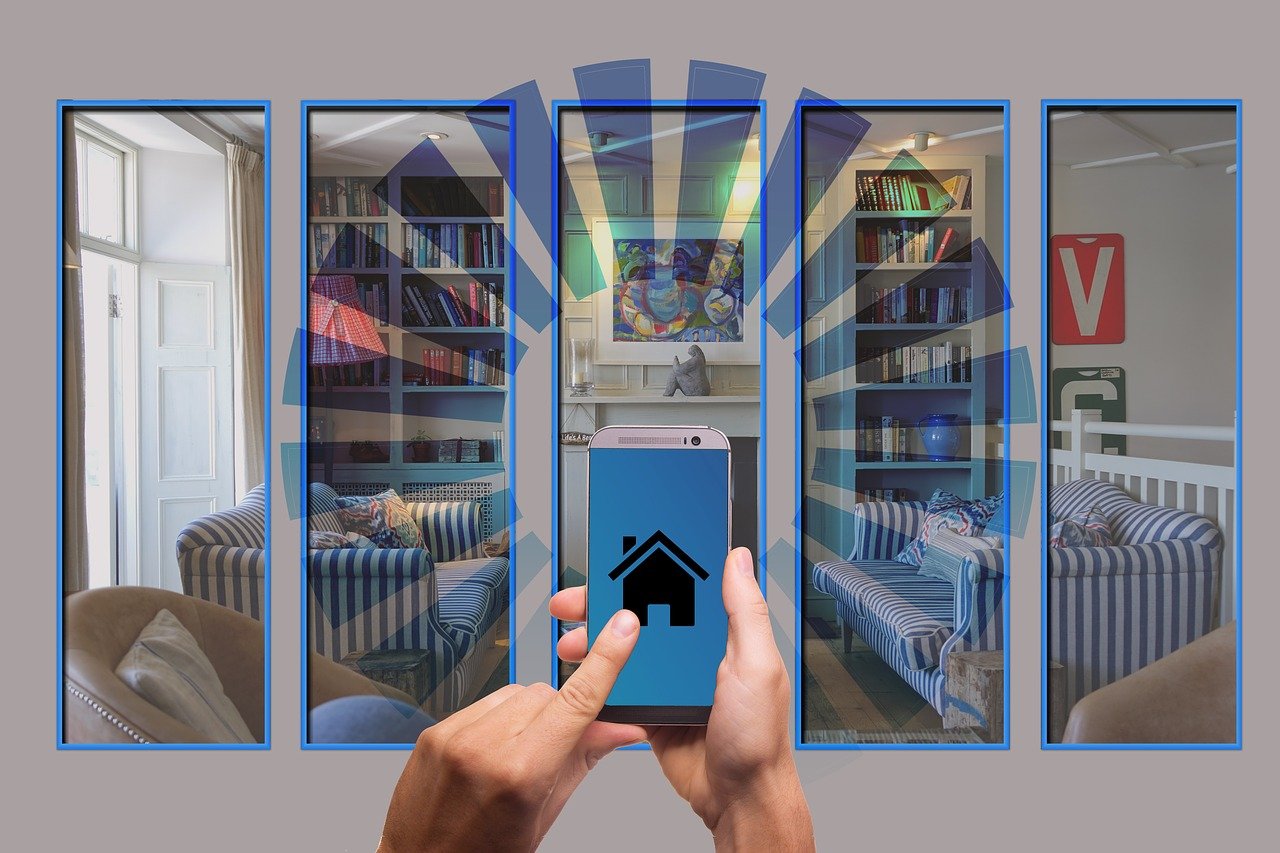
The use of IoT in homes, offices and workspaces has become increasingly popular, but one must be aware of the security drawbacks that their use entails.
One of the most dangerous situations could be a hacker injecting a malicious ransomware script that holds your smart home or office hostage until you pay up a ransom, which is usually very high.
Privacy concerns
Privacy concerns aren’t a new phenomenon in the world of Internet and the same is true for the Internet of Things. Personal data can be retrieved once the IoT network is up and running.
There are various tools available that detect the patterns in data and collect them. Gaining access to this data can result in its misuse and abuse.
Insecure interfaces
IoT makes use of many interfaces like the cloud, mobile and web for information which makes it efficient — yielding the best results.
But these interfaces are not very secure, and if any of these are surpassed, a hacker can get easy access to the devices in the network as the connection between these itself isn’t secure.
Insufficient security configurations
The Internet of Things ecosphere lacks a granular permission model that allows you to customise specific privileges for different users, i.e., to separate the regular users from the ones with administrative controls.
There is no option to alter security controls and makes personal information accessible to all of its users.
Poor physical security
An attacker can easily disassemble an IoT device and gain access to the storage component. Also, external ports or USB slots present for maintenance purposes can be used to access the data in that device.
If a hacker gets into your IoT network at home or office, they will be able to access information across the devices connected to that network.
Read more: 3 ways Google Assistant can help protect your home
Data security is crucial in any field. The Internet of Things ecosystem undoubtedly reduces human effort and saves time, but for now, it comes at a crucial cost – security and privacy of the user.
As the tech progresses, there will be many security protocol upgrades that will further secure IoT networks, but for the time being, it is necessary to understand the implications of setting up an IoT network in your workspace or home.