A potential watering-hole attack has been discovered on the Hunza News website, a regional news outlet covering Gilgit-Baltistan, a disputed region under Pakistan occupation. The attack targets Urdu-speaking users in the region, distributing a previously unknown Android spyware named Kamran.
Kamran’s espionage capabilities were identified when users attempted to download the Hunza News Android app from the Urdu version of the website. ESET detected the malicious app as spyware.
The Hunza News website, known for delivering news about the Gilgit-Baltistan region, has been active for over a decade, focusing on the region’s population of approximately 1.5 million.
Hunza News launched its official app in 2015 to provide content in a user-friendly way. However, as researchers found out, in the second half of 2022, the app was removed from the Google Play Store, and the news organisation had no app until January 7th, 2023.
ESET researchers revealed that a new app version has been available since at least March 21, 2023. This new version was not available on any app store, and users had to click on the download button on the website to get the app.
Notably, the English mobile version of the website does not offer any app for download, while the Urdu version on mobile prompts users to download the Android spyware. Both English and Urdu desktop versions also provide spyware, although it is incompatible with desktop operating systems.
The malicious Hunza News app appeared on the website between January 7 2023, and March 21, 2023. This period coincided with protests in Gilgit-Baltistan related to land rights, taxation concerns, power outages, and a decline in subsidised wheat provisions.
“With a high degree of confidence, we can affirm that the malicious app is specifically targeted at Urdu-speaking users who access the website via an Android device,” said Lukas Stefanko of ESET.
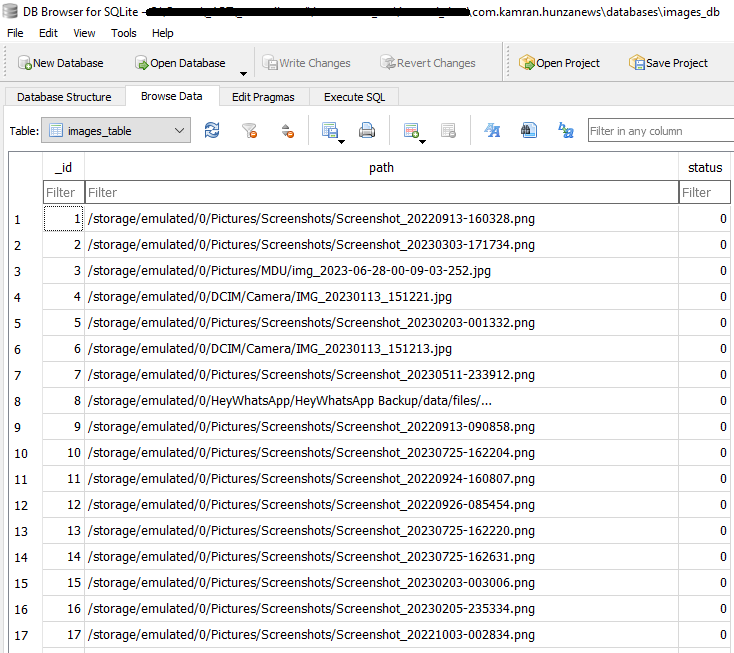
Victims of the attack include at least 22 compromised smartphones, with five located in Pakistan. The spyware, unique in its composition, gathers sensitive user data, including SMS messages, contacts, call logs, calendar events, device location and images.
Interestingly, researchers found that Kamran utilises Firebase as its command and control (C2) server, with data exfiltration occurring only when the user opens the app. The malware lacks remote control capabilities, repeatedly sending the same data to the C2 server.
In the News: Notorious cybercriminal group LockBit targets ICBC’s USA arm




