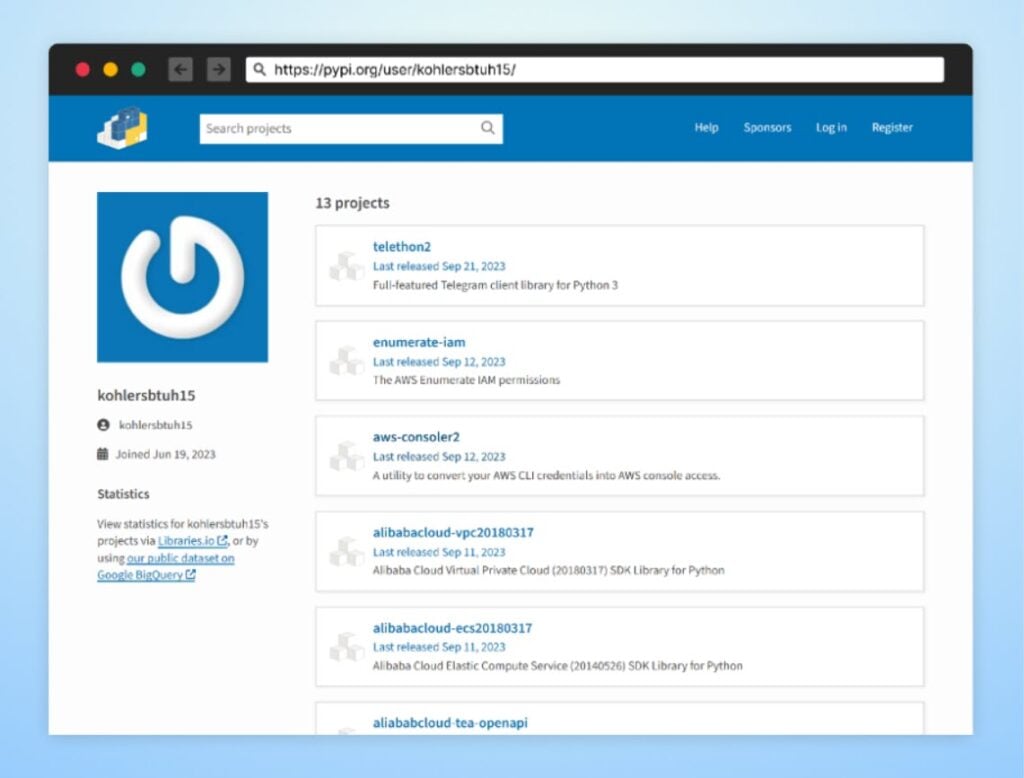
A malicious attacker operating under the pseudonym ‘kohlersbtuh15’ executed an attack against the open-source software community, specifically developers using Aliyun services (Alibaba cloud), Telegram, and AWS.
Cybersecurity analysts from Checkmarx studied the attack in detail. This attacker employed tactics, including Typosquatting and Starjacking, to upload deceptive and malicious packages to the PyPi package manager.
What sets this attack apart is the unique approach of embedding malicious code deep within the packages, within specific functions, allowing the code to remain dormant until a particular function is called during regular usage.
Typosquatting is a technique that capitalises on human error and the potential for developers to input incorrect installation commands. This technique is a significant component of the attack. The attacker published malicious packages with names similar to legitimate ones, tricking developers into unwittingly downloading them.
In some instances, malicious dependencies triggered hidden scripts to run in the background, while in others, the malicious code was directly embedded within the packages, masking the true nature of the software.
The attacker’s strategic use of Starjacking further complicated matters. Starjacking involved linking a package hosted on a package manager to an unrelated package’s GitHub repository, deceiving developers by making it appear trustworthy.
To maximise the attack’s reach, the attacker combined Typosquatting and Starjacking in the same packages, such as Telethon2, which mimicked the popular Telethon package with 69 million downloads.
The attacker copied the official Telethon package’s source code, embedding malicious code within the ‘telethon/client/messages.py’ file. However, the malicious code only activates when the ‘send message’ function is called, executing OS commands.
Another package of note was ‘enumerate-iam’ which exploited a popular GitHub repository called ‘enumerate-iam’. The attacker created a malicious Python package with the same name as the repository, embedding malicious code within a function to steal sensitive credentials.
This meticulously planned attack did not happen by chance. By targeting widely-used packages associated with platforms like Telegram, AWS, and Alibaba Cloud, the attacker aimed to compromise specific users and potentially affect millions. Beyond the immediate compromise of systems, this attack endangered the sensitive data associated with these platforms, including communication details from Telegram, confidential cloud data from AWS, and business-critical information from Alibaba Cloud.
The attacker’s strategy of hiding malicious code within specific functions is a double-edged sword. It bypasses conventional security scans designed to detect self-executing scripts and permits highly targeted attacks. unsuspecting developers or users unknowingly activate the malicious code when invoking these functions, making the attack discreet and remarkably effective.
Researchers have advised the members of popular project platforms such as GitHub to have a placeholder package on platforms like PyPi to guard against opportunistic attackers exploiting the absence of legitimate packages.
“Using malicious packages as dependencies in your code carries significant risks. In the best-case scenario, you may end up infecting high-privileged developer accounts within your network. If you are less fortunate, you could end up infecting your customers with compromised software releases,” said researchers.
In the News: ToddyCat APT group is using tailored loaders to deliver payloads




