Photo: Framesira / Shutterstock.com
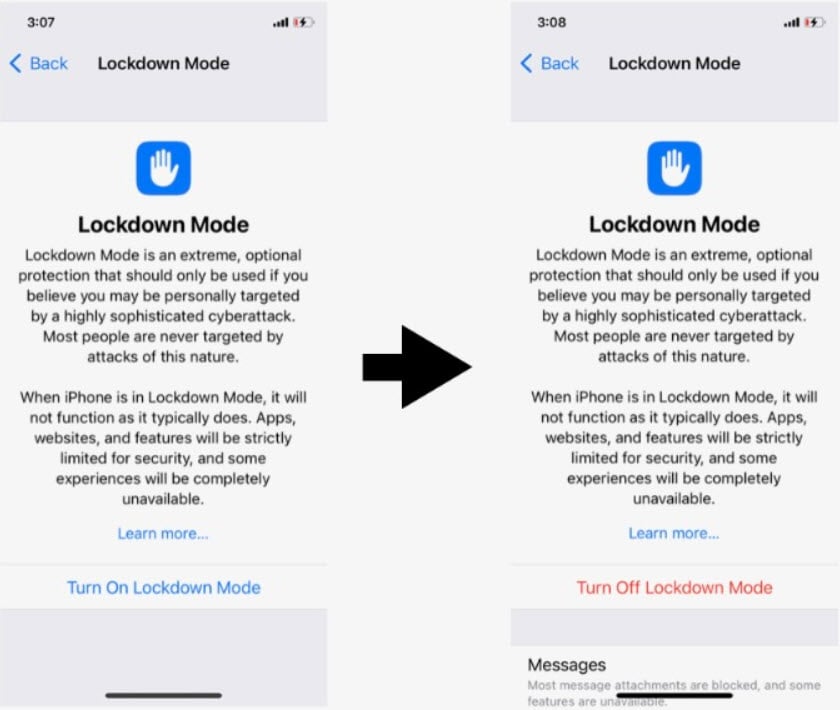
Scammers are using post-exploitation tampering techniques to tamper with the Lockdown Mode functionality of iPhones, thereby giving the user a false sense of security.
Cybersecurity researchers from Jamf revealed this technique in a blog post. The post-exploitation technique allows attackers to visually mimic Lockdown Mode without implementing protective measures. This could potentially deceive users, particularly high-profile targets like journalists, government officials, and executives, into thinking their device is secure when, in reality, it remains compromised.
Many people are confused regarding the nature of Lockdown Mode. The researchers cautioned that while Lockdown Mode is a valuable tool in preventing potential attacks, it does not function as an antivirus software. Lockdown Mode cannot detect existing infections or impede the operation of malware already on a compromised device.
Lockdown Mode only restricts the entry points for potential attackers rather than offering comprehensive security measures.
Researchers demonstrated that, on compromised devices, attackers can manipulate lockdown Mode, rendering it ineffective against malware. By exploiting the Settings app, attackers can initiate a visual representation of Lockdown Mode without activating the necessary security configurations, thus tricking users.
Attackers can manually override the user’s default database with commands like [[NSUserDefaults standardUserDefaults] setObject: [NSNumber numberWithBool: 1] forKey:@"LDMGlobalEnabled" inDomain: @"NSGlobalDomain"].
By targeting the -[PUILockdownModeController setLockdownModeGloballyEnabled:] method, attackers can replace its content using the method_exchangeImplementations Method Hooking technique, initiating a userspace reboot whenever a user attempts to activate Lockdown Mode.
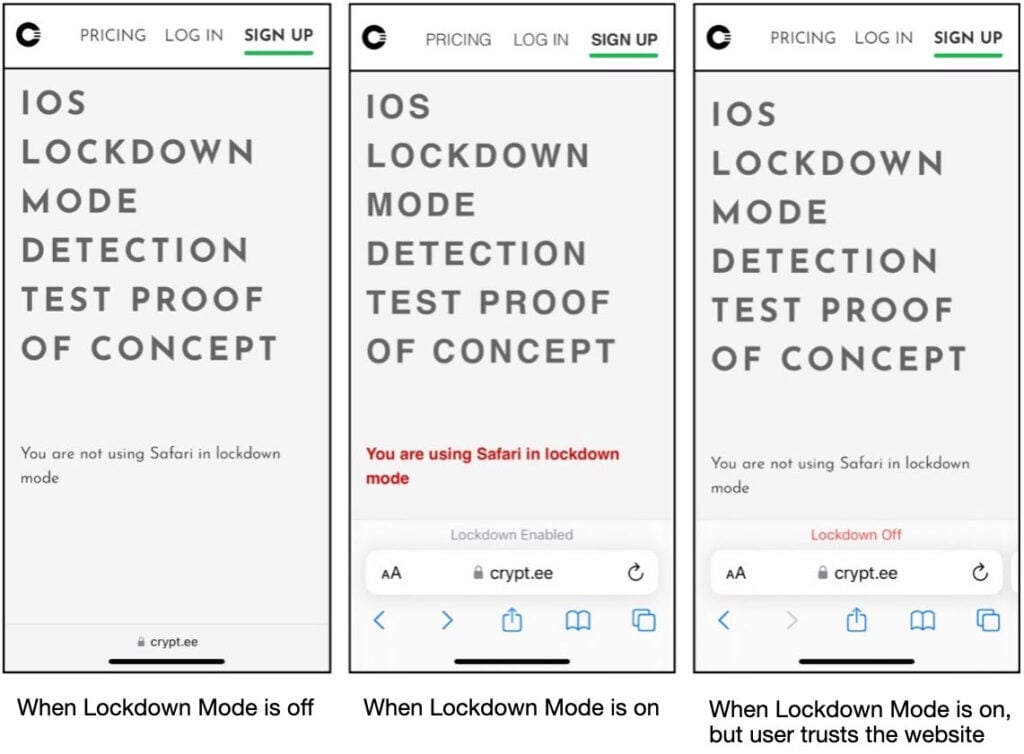
Furthermore, experts observed a Lockdown Mode vulnerability in Safri. Attackers can hook the +[WBSUIFeatureAvailability isLockdownModeEnabledForSafari] function to achieve the desired results.
Researchers found that up to iOS 16.5, there was no code to implement Lockdown Mode within the kernel. However, this changed with the release of iOS 17. With iOS 17, Apple elevated Lockdown Mode to the kernel level, enhancing its security by introducing a background daemon and a KEXT. With this move, Apple ensured that the changes made by Lockdown Mode in the kernel are more secure and irreversible without a system reboot.
The experts believe this vulnerability isn’t exploited in the wild and is only possible on a compromised device.
In the News: Atlassian patches four critical RCE flaws in multiple products




