A financially motivated crypto stealing campaign using the recently discovered ‘MortalKombat’ ransomware and a GO variant of the Laplas Clipper malware was spotted by Cisco Talos researchers. The campaign has been running since at least December 2022 and continues to attack individuals, small businesses and even bigger organisations looking to receive ransom payments in cryptocurrencies. Most of the victims are located in the US, with a smaller percentage located in the UK, Turkey and the Philippines.
MortalKombat is a novel ransomware that was only recently discovered in January 2023. There’s little known about its developers or operating model, but Talos researchers can assess with “high confidence” that it belongs to the Xorist family. Laplas Clipper, on the other hand, is a clipboard-stealing malware first discovered in November 2022.

The unidentified threat actor looks for victims by scanning the internet for victim machines that have an exposed RDP (Remote Desktop Protocol) port 3389. The scan is run on one of the two download servers that the operators run which also facilitates the MortalCombat ransomware.
Once a victim is found, the attack vector begins starts off with a phishing email that later evolves into a multi-chain attack ending in the attacker infecting the victim’s PC with either malware or ransomware, deleting evidence of malicious files and further covering their tracks.
As for the emails themselves, the attacker impersonates CoinPayments, a legitimate crypto payment gateway from a spoofed sender email stating that a crypto payment made by the victim has been declined with an attached ZIP file with a name resembling a transaction ID.

This malicious ZIP file contains a BAT script that downloads another ZIP file from the attacker’s hosting server, inflates it and inflates either the GO variant of Laplas Clipper malware or MortalKombat ransomware. The loader script then proceeds to run the downloaded malicious payload as a process on the victim’s machine and deletes the originally downloaded dropper files.
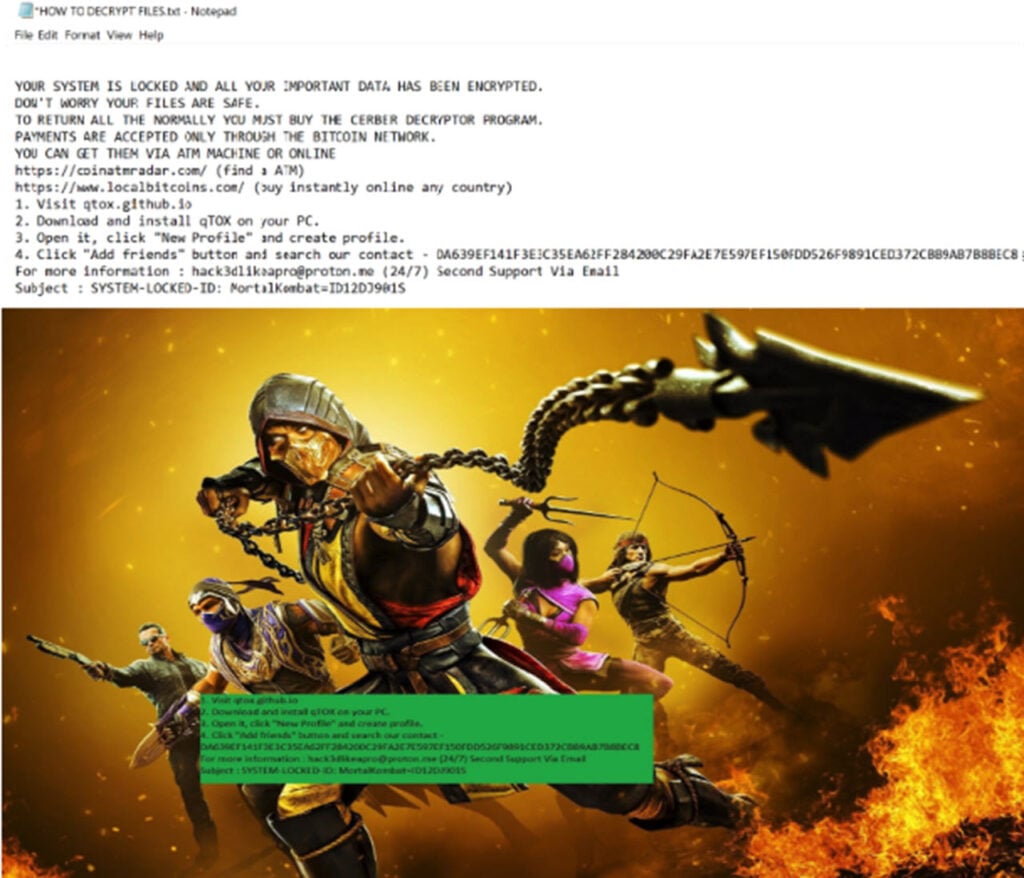
Once a victim is infected, the operators use the qTOX, an open-source instant messaging program freely available on Github to communicate with the victim. The program doesn’t monitor any communication channels either, making it rather appealing to cybercriminals.
So far, Talos researchers have discovered two download URLs run by the campaign operator. One is based in Poland and runs an RDP crawler to find victims while also supporting the MortalKombat ransomware. The other URL downloads the Laplas Clipper malware and communicates with the clipper bot.
In the News: Hyundai and Kia patch vulnerabilities revealed by TikTok




