A new ransomware strain has been discovered in the wild and attributed to Lazarus (APT-38), the infamous North Korea state-backed cybercriminal group. These strains and the corresponding links were found when analysing source code and artefact similarity with VHD Ransomware, linked to Lazarus as well.
In __ 2021, researchers from Kaspersky and Sygnia made the connection after seeing the two strains (VHD and TFlower) being deployed on victim networks using the MATA malware framework, exclusively used by Lazarus.
According to Christiaan Beek, lead threat researcher at cybersecurity firm Trellix, the string has also been found in similar ransomware families including Beef, PXJ and ChiChi with ZZZZ and Beef being near duplicates.
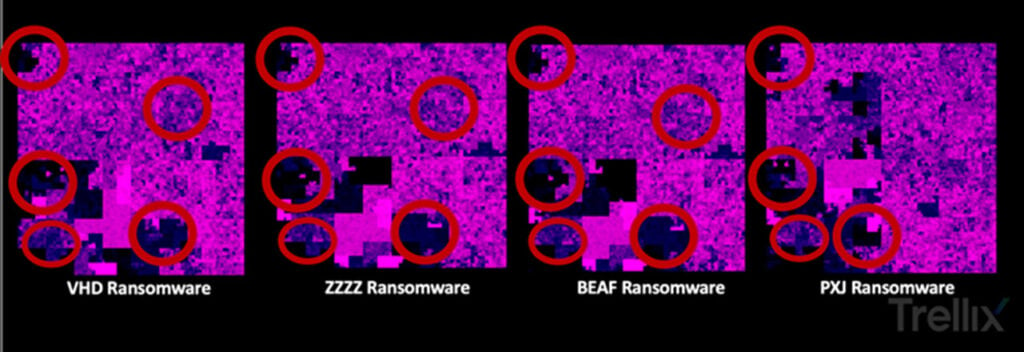
Similarities were discovered by the method of code visualisation, which pointed out immediate likeness in the Beef and ZZZZ as well as ChiChi and TFlower ransomware families.
The researchers attributed the strain to APT-38 by following the Bitcoin transaction chain of VHD ransomware. While there were no similarities in wallet addresses, both chains demanded small ransom payments. Based on this code similarity and ransom payment overlap, Trellix has attributed these families to Lazarus hackers with high confidence.
Additionally, when comparing ransomware notes, researchers found a common email address, semenov.akkim@protonmail.com was used by both ChiChi and ZZZZ ransomware families.

The targeted families in this research aren’t exactly widespread at the moment and have been attacking specific targets in the APAC region. Not much is known about the victims either because there were no leaks or negotiation chats, as is the common practice among these groups.
Lazarus has been known to attack financial institutions, traditional and crypto alike and get away with surprisingly big amounts. The group recently got away with $600 million from hacking the Ronin Bridge in March, was responsible for the Wannacry ransomware attacks and has been active since 2014.
In the News: Alexa voice data is used for ad targeting by over 41 3rd party ad networks




