The PlugX malware is still wreaking havoc on hundreds of thousands of devices across more than 170 countries, and it shows no signs of stopping. Despite the creators losing control, between 90,000 and 100,000 unique IP addresses send malware requests daily to a sinkhole server. These requests have been observed over six months, confirming the malware’s extensive reach and persistence.
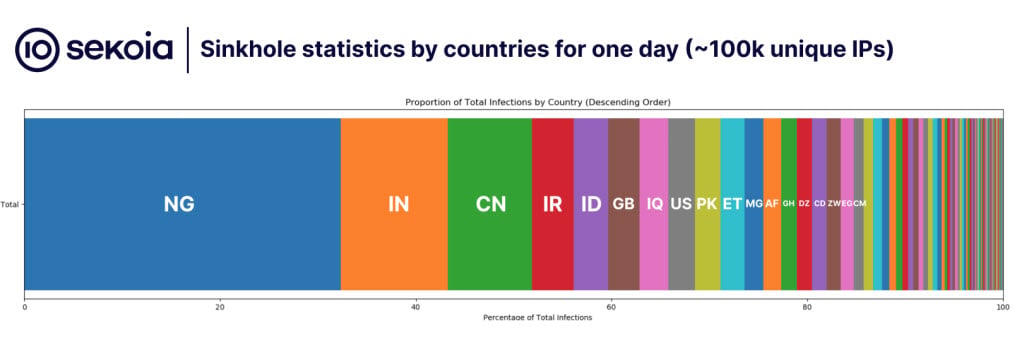
Researchers discovered that about 15 countries contribute over 80% of the total infections. Furthermore, they discovered that these countries have little in common, leading the experts to conclude that the malware must have originated from multiple patient zeros. Maximum infections were discovered in Nigeria, followed by India, China, and Iran.
The origins of PlugX trace back to its initial deployment in 2008 during a Chinese campaign targeting government-related users and specific organisations in Japan. Over time, this cyber weapon evolved, with notable instances such as the implementation of a wormhole component in July 2020 by the Mustang Panda intrusion set. This component allowed PlugX to propagate through connected USB flash drives, executing its infection chain when accessed by users, thereby expanding its reach across systems.
The zombie worm is vulnerable to takeover by any threat actor possessing interception capabilities. This allows them to assume control of the infected server and issue commands to repurpose it for nefarious purposes.
“In September 2023, we managed to take ownership of this IP address to a sinkhole that botnet. We initially thought that we will have a few thousand victims connected to it, as what we can have on our regular sinkholes. However, by setting up a simple web server we saw a continuous flow of HTTP requests varying through the time of the day,” the researchers said.
The operational strategy of the PlugX attack employs a multifaceted approach incorporating advanced techniques to infiltrate and endure within targeted systems. The attack typically initiates with an initial compromise of a system. This infiltration can occur through various channels, such as deceptive emails containing malicious attachments or links, exploit kits exploiting vulnerabilities in software, or physical access to introduce infected USB flash drives into a system.
Upon compromising a system, PlugX utilised a DLL-side loading technique for execution. This method manipulates a legitimate executable on the system to load a malicious or modified DLL file, which then executes PlugX’s core components. This manipulation enables PlugX to avoid detection and operate within the system’s environment.

PlugX employs multiple persistence mechanisms to ensure its sustained presence within the compromised system. It may establish registry keys or scheduled tasks for automation execution during system startup or user login, ensuring its continuity even after the system reboots.
The malware communicates with its command and control (C2) server using various communication protocols like TCP and HTTP. These protocols facilitate command transmission, data exfiltration from the compromised system, and reception of updates or additional payloads from the C2 server.
PlugX employs encryption and obfuscation techniques to evade detection and analysis in its communication protocols and payload delivery. This complicates interception and decryption by security researchers and tools, enhancing its stealth capabilities.
Upon activation, PlugX offers diverse functionalities to its operators, commonly known as threat actors or adversaries. These functionalities encompass remote command execution, file upload/download capabilities, file system exploration, data extraction, and persistence management, providing full control over the compromised system.
Notably, PlugX variants include a self-deletion mechanism (identified as 0x1005 in the research) that enables threat actors to remove PlugX from infected systems remotely. This mechanism conceals traces or avoids detection after objectives are fulfilled.
Despite countermeasures like sinkhole operations and remote disinfection strategies, mitigating PlugX remains challenging due to legal complexities, limitations in remote disinfection capabilities, and its persistent presence on infected USB devices.
In the News: LightSpy extends threat to macOS devices following iOS




