Researchers over at ComSec Computer Security group have discovered a new way to trigger Rowhamer bit flips on all DRAM devices, bypassing manufacturer safeguards with “little effort.”
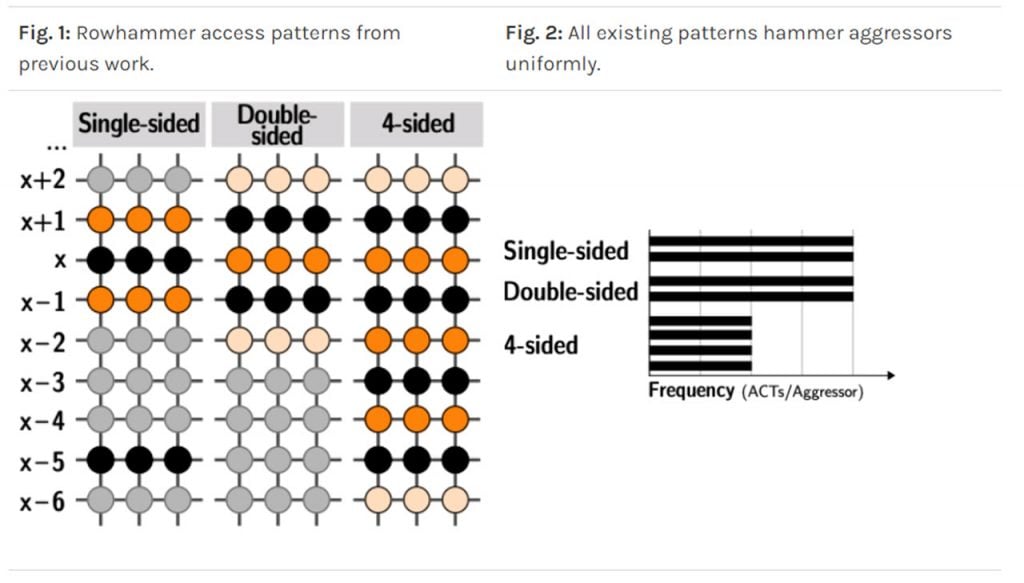
Rowhammer is a vulnerability primarily caused by leaked charges in DRAM cells, enabling an attacker to induce bit flips — turning 0s to 1s and vice versa in DRAM memory. This new technique, presented in a research paper published on Monday, uses non-uniform patterns which access two or more aggressor rows with different frequencies.
As a result, all 40 DIMMs in the test pool (selected at random) experienced bit flips. Previously, this number was at 13 out of a test pool of 42 from the same researchers.
In the News: FBI email servers compromised; fake warnings sent to 100,000+ victims
Flipping RAMs and causing damage
The new non-uniform patterns were implemented using a custom-built ‘fuzzer’ — a software that detects bugs by injecting deformed data into a piece of hardware or software in a semi-random way. This ‘fuzzer’, called blacksmith, is effective against about 94% of the DRAM modules on the market.
These new non-uniform patterns are somewhat effective against TRR or Target Row Refresh — a countermeasure against Rowhammer attacks baked in by manufacturers. While it works differently for every manufacturer, in general, TRR tracks the number of times each row is accessed and recharges neighbouring rows if it suspects anything shady happening.
This technique has been proven ineffective now puts pressure on manufacturers to protect recent types of chips that were previously thought to be safe from this class of attacks.
The attack has serious consequences as well. Researchers were able to gain unrestricted access to all physical memory by flipping bits in the page table entry, which is used to map memory address locations. Rowhammer was also used to extract a 2048-bit encryption key out of memory and reproduce the crypto key attack.
Apart from this, these attacks allow untrusted programs to gain unrestricted system access, bypass security restrictions or sandboxes and even root or infect Android devices. According to the researchers, simulations suggest that other attacks are also possible.
In the News: Microsoft adds 76 new games to Xbox backward compatibility program





