Researchers identified critical security flaws in Samsung devices’ boot chain system. The vulnerabilities were tracked in two components of Samsung Galaxy devices, specifically model A225F.
The vulnerabilities, CVE-2024-20832 and CVE-2024-20865, affect the components Little Kernel (third bootloader) and Secure Monitor (high-privilege software). The boot chain on Android starts with a Boot ROM, which initiates the bootloader. The bootloader then loads the kernel, which is responsible for booting the Android OS.
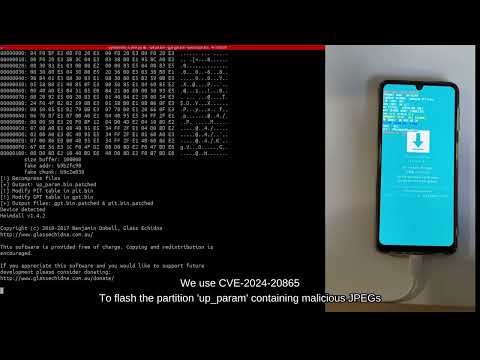
CVE-2024-20832 is a flaw caused by heap overflow in Little Kernel’s JPEG parser. It can be exploited to execute kernel codes that persist through reboots and factory resets. The second weakness, CVE-2024-20865, allowed researchers at QuarksLab to bypass Odin’s authentication system, which is the Samsung device recovery tool.
By using the two flaws together, malicious code can be executed in the Little Kernel, which is responsible for verifying and booting an Android device, without being removed after a reset.
This could be used to gain root-level Android access, alter the ‘up_param’ partition containing critical JPEG files, disable boot image verification, and extract personal data, including Android Keystore encryption keys. The researchers said, “But, by design, some components like the keys of the Android Keystore are not reachable, even by root,” as they are protected in the Secure World’s memory.
The third and fourth vulnerabilities, identified as CVE-2024-20820 and CVE-2024-20021, were found in the ARM Trusted Firmware, also known as Secure Monitor. These flaws could be used to map arbitrary physical memory. By chaining the flaws, threat actors could bypass the Android security model to access protected components such as the Android Keystore. The exploit chain shows the four bugs that enabled code execution in Little Kernel through USB.
The security breach impacts multiple devices in the Galaxy A series, with proof-of-concept demonstrations on GitHub. The exploit compromises a device’s security chain from the bootloader to the operating system level. The researchers presented their findings at BlackHat USA 2024, which reflects critical security implications for Samsung devices with Mediatek SoCs.
In the News: WhatsApp might expose your device’s OS and other sensitive info