Threat actors attempted to leverage the vulnerabilities in SQL Server instances for lateral movement, a strategy previously unseen within SQL Server instances. While this lateral movement technique has been observed in other cloud services, such as VMs and Kubernetes clusters, its emergence within SQL Server instances is significant.
Microsoft’s cybersecurity researchers published a report detailing the intricacies of the attack.
The attackers initiated their offensive by exploiting a SQL injection vulnerability within an application hosted in the target’s environment, ultimately granting them access to a Microsoft SQL Server instance deployed in an Azure Virtual Machine (VM). Subsequently, the attackers leveraged this elevated access to infiltrate further into the cloud resources, capitalising on the server’s cloud identity.
After the initial SQL injection attack, the attackers gathered intelligence about the host, databases, network configurations, table names, schemas, and permissions.
The attackers exploited their acquired elevated access to enable the cmdshell command, which allows the execution of operating system commands through SQL queries. With this capability, they conducted a series of OS commands, operating like a shell on the host.
They used rudimentary methods such as directory enumeration, process listing, and network share inspection. Additionally, they downloaded executables and compressed PowerShell scripts, primarily relying on PowerShell commands, scripts and modules for their actions.
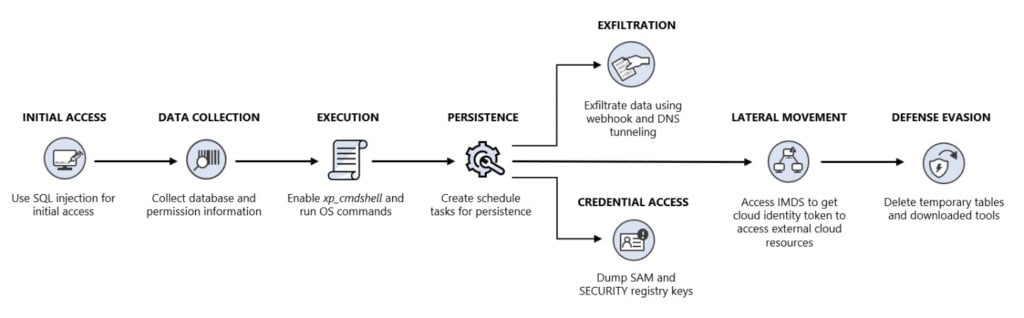
To maintain persistence, the attackers employed a scheduled task to launch a backdoor script and attempted to acquire credentials by extracting the SAM and SECURITY registry keys. They employed a unique method for data exfiltration by using a publicly accessible service called 'webhook.site' to conceal their outgoing traffic within a seemingly legitimate platform.
The attackers also attempted to exploit the identity of the SQL Server instance by accessing the instance metadata service (IMDS) and obtaining the cloud identity access key. While they did not succeed due to an error, this tactic highlights the potential risk of insufficiently securing cloud identities.
The attack triggered multiple alerts from Microsoft Defender for SQL, resulting in Microsoft’s investigation. Currently, there is no evidence that the attackers successfully moved laterally to cloud resources.
The attack represents a shift in cybercriminals tactics, focusing on exploiting cloud identities associated with cloud resources. Prominent cloud servers, including Azure, rely on managed identities to streamline authentication for cloud resources and services. While these managed identities offer convenience, security, and efficiency, they also introduce potential vulnerabilities attackers can exploit.
In the News: Wattpad wraps up Paid Stories for freemium Wattpad Originals




