Notorious cybercriminal threat actor TA577 has begun employing a new and sophisticated attack chain to achieve an unusual objective of stealing NT LAN Manager (NTLM) authentication information.
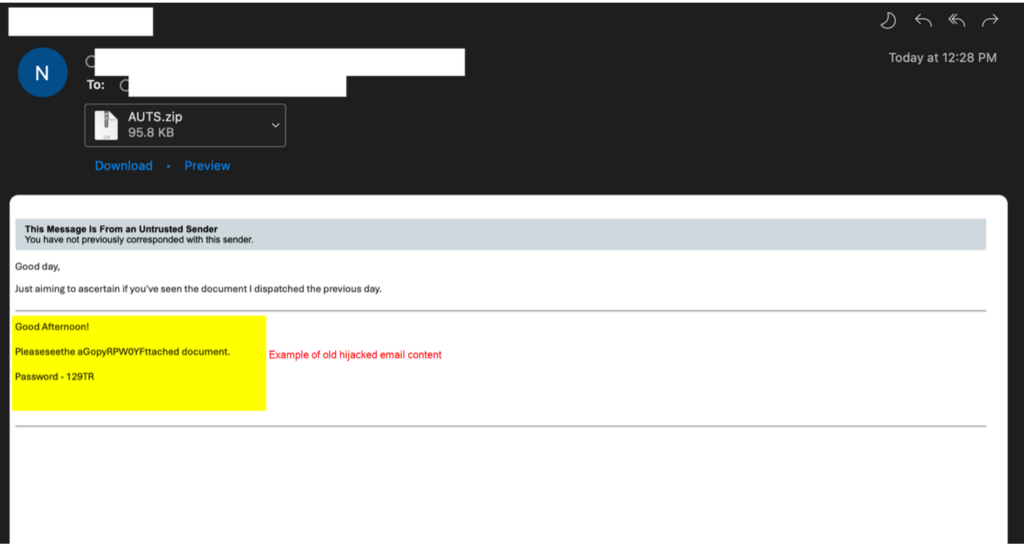
Researchers from Proofpoint detected at least two campaigns orchestrated by TA577, both executed on 26 and 27 February 2024. These campaigns targeted hundreds of organisations globally, utilising tens of thousands of messages. The attackers employed a technique known as thread hijacking, replying to previous emails, and embedding zipped HTML attachments to carry out their nefarious activities.
Each compressed .zip attachment carried a unique file hash, with customised HTML files tailored for specific recipients. Upon opening, the HTML triggered a system connection attempt to a Server Message Block (SMB) server through a meta-refresh to a file scheme URL ending in .txt.
This automatic connection sought an external SMB resource owned by the threat actor, aiming to capture NTLMv2 Challenge/Response pairs and pilfer NTLM hashes.
Proofpoint notes that, at this point, no malware delivery has been observed from these URLs. This led the researchers to believe that TA577’s primary objective is to harvest NTLMv2 Challenge/Response pairs based on the attack chain’s characteristics and tools used.
The use of the open-source toolkit Impacket on the SMB server was identified, evidenced by the default NTLM server challenge and the default GUID observed in the traffic — practices uncommon in standard SMB servers.
The compromised NTLM hashes could be exploited for password cracking or facilitate ‘Pass-The-Hash’ attacks within the targeted organisation. TA577’s delivery of malicious HTML within a zip archive is noteworthy, as it generates a local file on the host. Interestingly, the researchers found that the attack would not be effective on Outlook mail clients patched since July 2023 if the file scheme URL were sent directly to the email body.
Researchers have attributed the attack points to TA577, a prominent cybercrime threat actor and a former major affiliate of the Qbot botnet. Known as an initial access broker (IAB), TA577 has been associated with follow-on ransomware infections, including the notorious Black Basta.
However, the recent campaigns indicate a shift towards delivering Pikabot as an initial payload. This revelation is significant as researchers have traditionally observed TA577 delivering malware without employing the demonstrated attack chain for NTLM credential theft, marking a departure from their usual modus operandi.
Proofpoint has advised users to take preventive measures, such as deploying blocking outbound SMBs to prevent exploitation.
In the News: India mandates government approval for AI models; issues clarification after uproar




