A novel exploit in SSH internet standard, Terrapin, allows hackers to perform Prefix Truncation attacks, tweak the sequence numbers during a handshake, and discreetly delete messages between the client and the server.
SSH is a fundamental internet standard that is crucial in providing secure access to network services. Terrapin, however, focuses on breaking the integrity of SSH’s secure channel by manipulating sequence numbers during the handshake.
This nefarious technique allows attackers to selectively remove messages from the client or server, downgrading the connection’s security without detection. The severity of the Terrapin attack is reflected in the assignment of three CVE numbers:
- CVE-2023-48795: General protocol flaw
- CVE-2023-46445: Rogue Extension Negotiation attack in AsyncSSH
- CVE-2023-46446: Rogue Session attack in AsyncSSH
Researchers Fabian Baumer, Marcus Brinkmann, and Jorg Schwenk from Ruhr University exposed the attack in a research paper.
Although the attack technique is rare and was only mentioned once in 2015, it was never used on such a large scale. Researchers found that the SSH was not protecting the full handshake transcript as the signature was formed only for the fixed list of handshake messages and not for the full list. SSH does not restructure sequence numbers, allowing manipulation of these sequence numbers before the handshake.
Based on these two observations, researchers explained that SSH connection is vulnerable to Sequence number manipulation, Prefix Truncation attacks, Extension Negotiation Downgrade attacks, Rouge Extension attacks, and Rogue Session attacks.
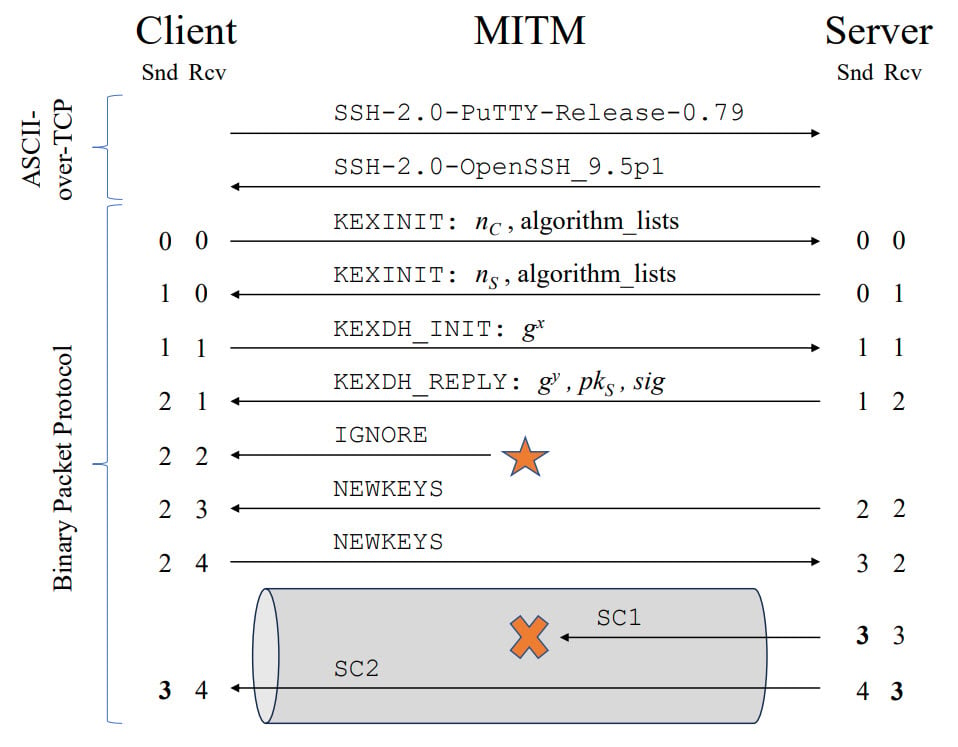
To execute the Terrapin attack, a Man-in-the-Midle attacker needs to intercept and modify the connection’s traffic at the TCP/IP layer. The vulnerability is exacerbated when the connection is secured using ChaCha20-Poly1305 or CBC with Encrypt-then-MAC encryption modes, which are prevalent across SSH sessions globally.
Explaining the intricacies of the attack, researchers delved into the attack sequence that comprises two steps:
- RcvIncrease technique: The attacker employs this technique to manipulate sequence numbers by injecting the ‘IGNORE’ message to the client before transmitting the ‘NEWKEYS’ message.
- Deletion of server’s message: Following the sequence number manipulation, the attacker deletes the server message.
Since the key exchange does not safeguard the handshake transcript from the insertion of ‘IGNORE’ messages, the integrity of handshake authentication remains uncompromised. Researchers also introduced a more generalised form of the attack, the (NS, NC)-Prefix Truncation Attack. In this broader attack, the adversary can delete any NS initial messages sent from the server and NC initial messages sent from the client within a single attack.
To assist users in determining if their SSH server or client is susceptible to the Terrapin attack, researchers have provided a vulnerability scanner in Go, available on GitHub.
In the News: Rhysida leaks 1.67 TB of Insomniac Games’ internal data






