An anonymous whistleblower angered by Putin’s invasion of Ukraine has leaked a set of files dating from 2016 to 2021 detailing Putin’s cyberwarfare plans both domestically and across international borders. The set of files dubbed the Vulkan files, is thousands of pages long and details how a seemingly usual-looking cybersecurity consultancy company Vulkan has been working for the Russian military and intelligence agencies to support hacking operations, training operatives, spreading disinformation and even controlling sections of the internet.
The company’s work has been linked to the federal security service, otherwise known as FSB, as well as the operational and intelligence decisions of Russia’s armed forces known as GUO and GRU and the SVR, the Russian foreign intelligence division.

Days after the Russian invasion of Ukraine began last year, the whistleblower reached out to German newspaper Süddeutsche Zeitung, claiming that the GRU and FSB are hiding behind Vulkan. The source further shared the data and even more information with another German investigative startup Paper Trail Media. Following this, journalists working for 11 media outlets, including the Guardian, Washington Post and Le Monde investigated the files in a consortium led by Paper Trail Media and Der Spiegel.
Five western intelligence agencies have confirmed that the Vulkan files appear to be authentic, containing emails, internal documents, project plans as well as budgets and contracts. Google-owned Mandiant also helped interpret the documents, which it also thinks are legitimate, though not unequivocally. Despite all the investigation, it’s still not known whether or not the Vulkan-made tools exposed in the leaks have yet been used in real-world attacks in Ukraine or elsewhere.
In the News: India is looking for spyware alternatives due to NSO PR problem
What are Vulkan and its cyberwarfare tools all about?
Vulkan was founded by current CEO Anton Markov and Alexander Irzhavsky in 2010. Both of them are graduates of St Petersburg’s military academy serving with the Russian army and rising to the ranks of captain and major respectively.
With both founders already having a good foothold in the Russian military, Vulkan came to be a part of the Russian military-industrial complex. Vulkan’s launch was assisted by the fact that Russia was looking to expand its cyberwarfare capabilities. As Sergei Shoigu, the man in charge of the Ukraine war, was appointed the minister of defence in 2012, the Guardian reports he immediately wanted cyber troops that reported directly to him.
Vulkan meanwhile had already received special government licenses to work on classified military projects and state secrets since 2011. It’s a part of roughly 12 private companies that have access to sensitive Russian projects.
Vulkan also works with what’s possibly the Kremlin’s most infamous cyberwarfare unit called Sandworm. Tools developed by the company and exposed in these files have been used to carry out several major cybersecurity attacks including an energy blackout in Ukraine, the disruption of the Olympics in South Korea as well as the creation of the NotPetya malware, the most economically destructive malware in history.
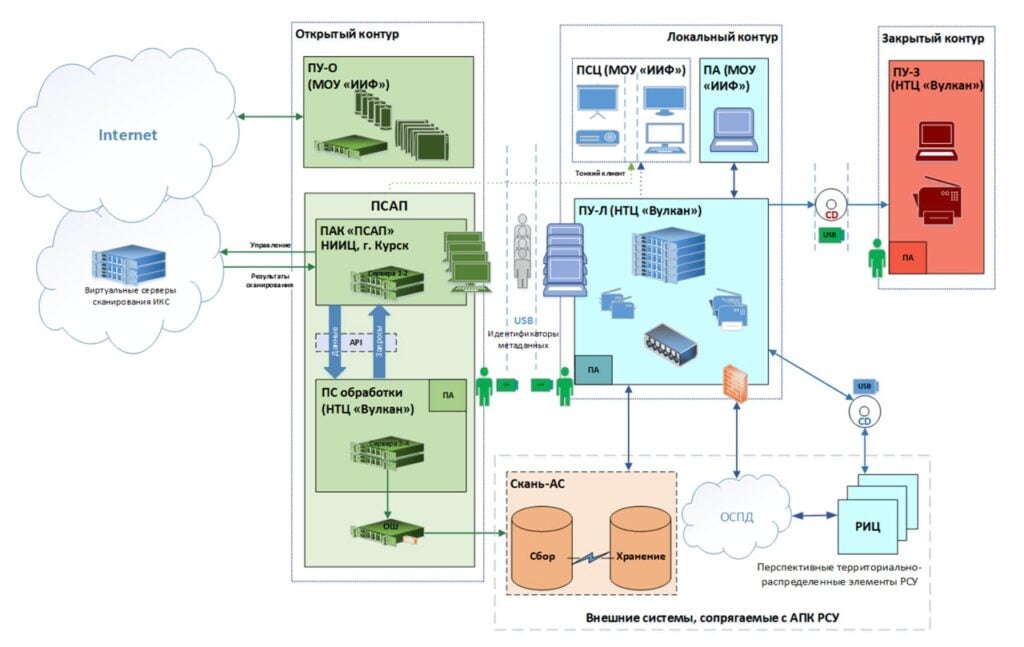
Out of the tools that the files list, one is called Scan-V and is meant to scan the internet for vulnerabilities, storing its findings for later analysis and exploitation. Another one called Amezit is a framework used to control online information as well as “manipulate public opinion, enhance psychological operations, and store and organize data for upstream communication of efforts”, according to Mandiant.
Finally, another tool called Krystal-2B is used as a training platform in conjunction with Amezit to coordinate attacks on transportation and utility infrastructure.
Gabby Roncone, a cybersecurity researcher with Mandiant who dug into the files says the projects contracted by Vulcan seem to support the broader strategic goals of information confrontation, a strategy that has largely influenced Russian cyberwarfare in Ukraine.
John Hultquistvice presidentnt of intelligence analysis at Mandiant also pointed out that the documents suggest that “Russia sees attacks on civilian critical infrastructure and social media manipulation as one and the same mission, which is essentially an attack on the enemy’s will to fight”.
In the News: India is looking for spyware alternatives due to NSO PR problem




