The devices around us are getting smarter by the day — from speakers to lightbulbs, everything is now interactive and connected bringing a new world to life. One which we could only dream of until now.
The onset of IoT has put home automation in the minds of consumers and companies alike. More and more people are getting their hands on these smart appliances and turning their houses into smart ones.
All of this, however, comes at a cost. The cost, literally and figuratively, is high as not only are these appliances expensive at the moment but can also pose some severe privacy threats.
Also read: What are Cyber-Physical Systems and the technologies that enable it
Smart appliances
Voice-activated light bulbs, fingerprint padlocks, smart speakers that you can talk to are perhaps the best-known examples of smart appliances.

These devices form an interconnected network between themselves, allowing the user to control multiple devices from a single access point.
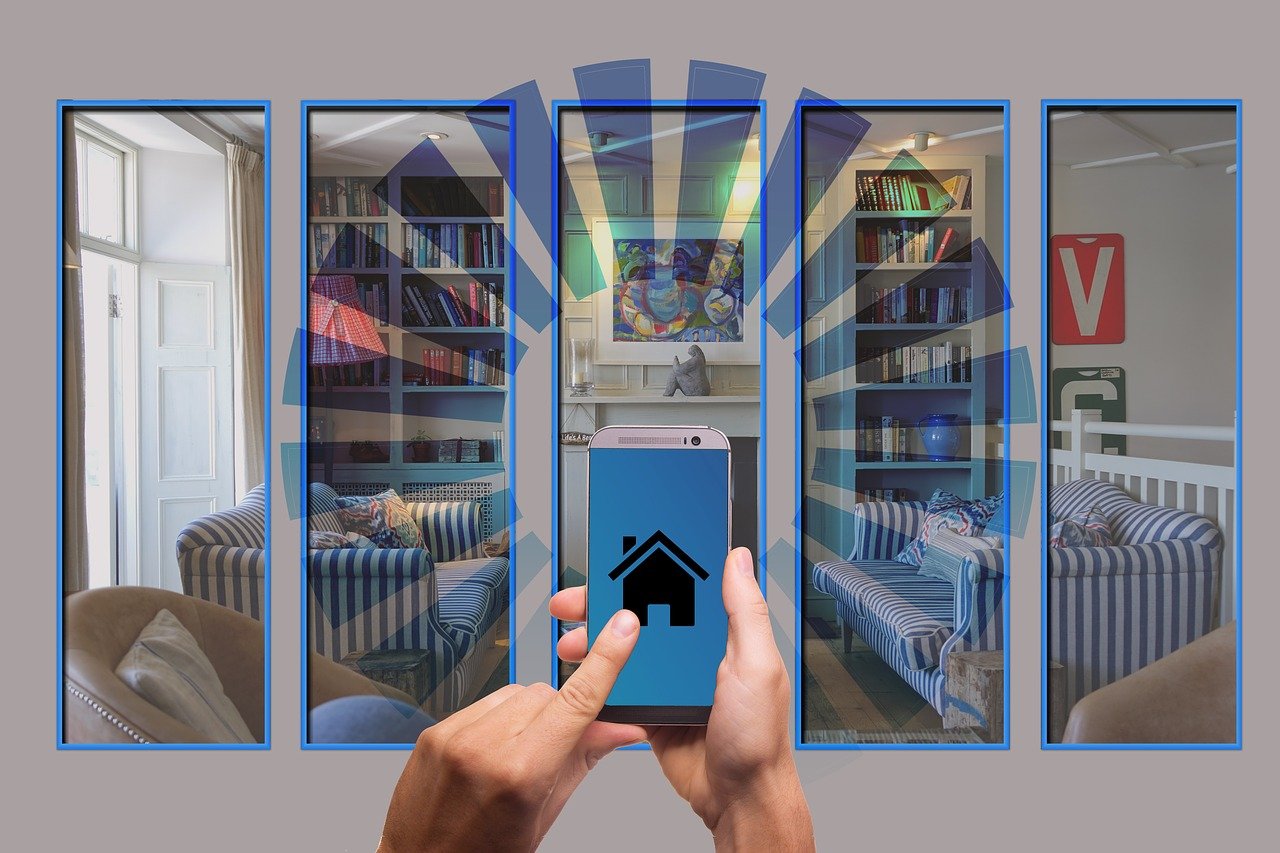
This network is called the IoT (Internet of Things). It is connected to the internet that allows for all kinds of cool things to happen. A user not only can control them remotely using their smartphone or any other device but can also talk to them.
Usually, the network looks something like this — all smart devices in a house (lights, fans switches) are connected to a central control point (e.g. smart speakers like Amazon Echo or Google Home). This central point, in turn, is connected to the internet.
All the user has to do is talk to their smart speaker (which has an inbuilt personal assistant like Alexa, Cortana, Siri, Google Assistant and more), and they can control all things connected to it.
The threats
IoT can be considered in its infancy and is still a developing technology. Most of the protocols used to communicate between these devices are several years old and have already been cracked.
That means that it is possible for an intruder to intercept data being shared between these devices. This can also be a potential entry point to your home or office network.
Having gained access to your smart home network, an intruder can get into any other device which directly puts you into the line of fire.
The biggest concern, however, is the smart speaker itself. These speakers have array style microphones designed to pick up your voice from a variety of angles and loudness. They can hear you across the rooms, even if you speak in a low pitch.
Some of these smart speakers even have built-in webcams. While this feature might be beneficial in some scenarios, this forces us to entertain the possibility that you might be under watch as well.
There may or may not be physical vulnerabilities on these speakers too. For example, the Amazon Echo’s 2015 and 2016 models can be exploited by using 18 debug connection pads, accessible by removing the rubber base from the device.
Questions have been raised on whether or not companies which design these products record us or not. The answers are not so convincing.
Apart from potentially being used to eavesdrop, these smart speakers may or may not have other vulnerabilities that might put you at an even higher risk.
Also read: 4 critical security threats the IoT boom poses
The solution
Yes, having an automated home is cool but keeping it safe is equally essential. As IoT continues to grow and expand, companies are making their products more secure. Newer protocols are being introduced with enhanced security options to keep hackers at bay.

Devices are also getting hardware/design upgrades. They are being designed in such a way that even their internals are inaccessible in case of a physical hack. Most smart speakers also offer a mute button that turns off the mic.
The security of your home or office network is also a factor in determining how secure is your smart home network. A vulnerable router might just lay waste to any software/hardware updates that your smart appliances might be equipped with — so, it’s equally important to make sure the peripherals connected to your smart home are secure too.
So be safe and Alexa, play Despacito!
Also read: 9 IoT Security Solutions to safeguard your network






