BlackLotus UEFI bootkit, sold for $5000 on hacking forums, can now take over and bypass Windows 11 Secure Boot — a threat that is often advertised but seldom realised.
Given the sheer number of UEFI vulnerabilities discovered in Windows OS in the past few years, and Microsoft’s slow review and patch process, UEFI boot kits are a powerful tool that could allow an attacker to gain full control over the OS, including the ability to disable its security features such as BitLocker, HVCI, and Windows Defender.
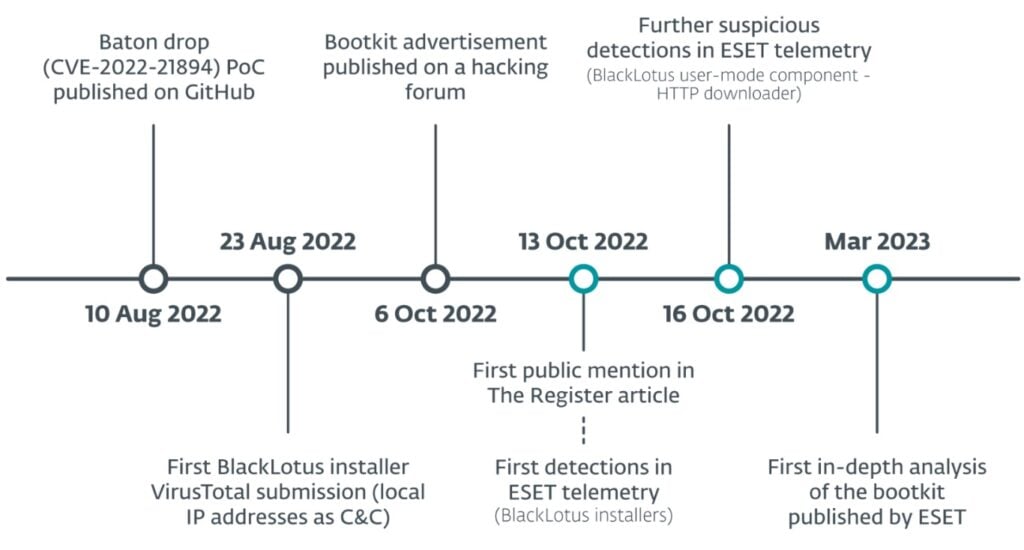
The BlackLotus malware has been sold on hacking forums since at least October 2022 for $5000, as spotted by security researcher Sergey Lozhkin. According to ESET researchers, the malware can run on the “latest, fully patched Windows 11 systems with UEFI Secure Boot enabled” and “is the first publicly known, in-the-wild abuse of this vulnerability”.
While Windows’ Secure Boot is typically in place to prevent unauthorised software from running, the year-old UEFI vulnerability (CVE-2022-21894) targeted by BlackLotus allows it to load before the booting process initiates — before the OS or its security tools can launch and take counter action. Microsoft patched the vulnerability, but the affected signed binaries can still be exploited as they haven’t been added to the UEFI revocation list.
Once the malware is installed, the bootkit deploys a custom kernel driver that protects the bootkit from being removed, among other things. An HTTP downloaded is also launched that enables communication and can also load additional user-mode or kernel-mode payloads.
Typically, malware with such capabilities sold on hacking forums are bogus files with tall claims, advertised by scammers to scam their peers. However, BlackLotus seems to deliver on its promise and isn’t a mere scam.
While the malware hasn’t been linked to a nation-state, the researchers noted that the malicious bootkit doesn’t proceed with the deployment if the compromised machine is found in one of the following locations: Moldova, Russia, Ukraine, Belarus, Armenia and Kazakhstan.
The researchers also didn’t find many cases of BlackLotus being used by cybercriminals but fear that since the vulnerable drivers are still not revoked, this could lead to a mass attack. UEFI boot kits aren’t common, and so far, only a few have been discovered, including ESPecter and FinSpy boot kits.
“The low number of BlackLotus samples we have obtained, both from public sources and our telemetry, leads us to believe that not many threat actors have started using it yet. But until the revocation of the vulnerable bootloaders that BlackLotus depends on happens, we are concerned that things will change rapidly should this bootkit gets into the hands of the well-known crimeware groups, based on the bootkit’s easy deployment and crimeware groups’ capabilities for spreading malware using their botnets,” the researchers noted.

In the News: Trezor users baited with fake data breach notifications




