CamScanner, a popular image to PDF creator and OCR app on Android’s Play Store with over 100 million downloads, was found shipping with malicious malware that can show ads and even sign up users for paid subscriptions, among other intrusive things.
CamScanner wasn’t a malicious app, to begin with, and sustained their business via in-app ads as well as purchases. But Researchers at Kaspersky found out that the recent versions of the app had a trojan dropper (module name: Trojan-Dropper.AndroidOS.Necro.n) which would extract malicious modules from the app’s resources that could run pop-up ads and scam people.
Soon after the malicious module was found, the researchers revealed their finding to Google, who removed the app from the Play Store. Camscanner’s developers, CC Intelligence, also have CamCard and Qixin apps on the Play Store.
The researchers also found that the malicious code had been removed with the latest CamScanner update, however, they also pointed out that “versions of the app vary for different devices, and some of them may still contain malicious code”.
Almost a month back, on July 29, CamScanner tweeted that those users who had received an anti-virus warning should upgrade their security software. On August 5, they tweeted enquiring whether their users based in India were having issues with the latest version of the app. This indicates that the developers surely had an idea that there’s an issue with the app but it’s still uncertain that the addition of the malicious module was the dev’s doing or not.
The paid version of the CamScanner app is available on the Play Store, but it has been subjected to much heat over the past few months due to their change in the subscription plan from a one-time license to a monthly subscription, without even informing their active paid users.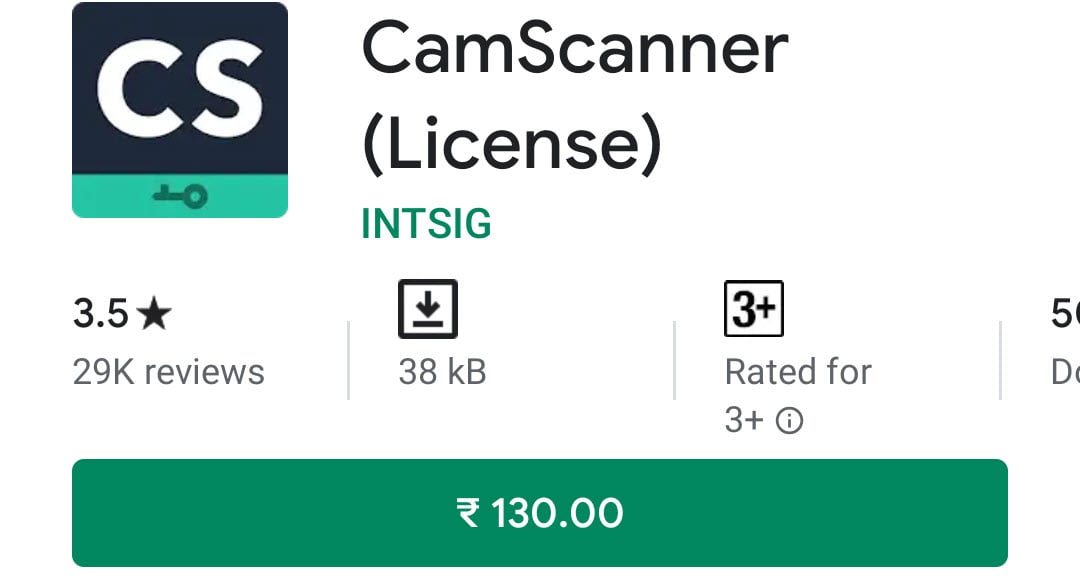 We’ve reached out CamScanner for a comment and will update it here when we receive a reply.
We’ve reached out CamScanner for a comment and will update it here when we receive a reply.
Google Play Store has millions of apps which are updated frequently and we’ve seen it happen quite often that the developers insert a malicious code in their apps, usually to fetch them more money by displaying intrusive ads and at some other times even screen logging or keylogging to get their hands over personally identifiable information, including financial data.
Earlier this month, active adware was found on 85 photography and gaming apps on the Google Play Store that were collectively downloaded over 8 million times. Adware has become an increasing nuisance, which is propelled by the poor app standards of the Play Store.
In July, researchers found 1000+ apps with millions of downloads which were snooping in on user data. Earlier this month, Android rolled out a security patch which fixed severe vulnerabilities on the devices powered by Qualcomm chipsets that allowed a third-party to attack the device over a WiFi network.




