Attackers accessed Cisco’s corporate networks in May after an employee’s personal Google account was compromised. The company disclosed the breach on Wednesday after a list of files accessed during the breach appeared on the dark web on August 10. A ransomware gang named “Yanluowang” claimed responsibility for the attack.
Cisco’s Security Incident Response (CSIRT) and the company’s cybersecurity intelligence group Cisco Talos noted that the only data exfiltrated was from an account with a cloud storage locker box associated with the compromised employee’s account. The leaked data dump is reportedly 2.75GB and contains around 3700 files.
That said, the attacker spent some time inside the company’s network infrastructure. Talos confirmed that the attacker gained access to Cisco’s networks, successfully authenticating to the company’s VPN and enrolling several devices for multi-factor authentication (MFA).
Cisco also published a statement clarifying that the breach did not impact its business, including Cisco products and services, sensitive customer data or employee information, intellectual property or supply chain operations. The company also added that it had been “actively collecting information” on the threat actor prior to disclosure and why it disclosed the information so late.
In the News: Microsoft confirms zero-day being exploited on Windows 10, 11 and Server; Patch issued
A close call with ransomware
After gaining access to the employee’s personal Google account, the attackers used voice-phishing techniques where an attacker impersonated a trusted organisation seeking to help the employee until they accepted a fake MFA notification that gave attackers access to Cisco’s VPN.
Once inside, the attackers gained access to Citrix servers and were eventually able to access domain controllers gaining domain admin privileges. They then used tools like ntdsutil, adfind and secretsdump to extract data and install a backdoor, among other payloads.
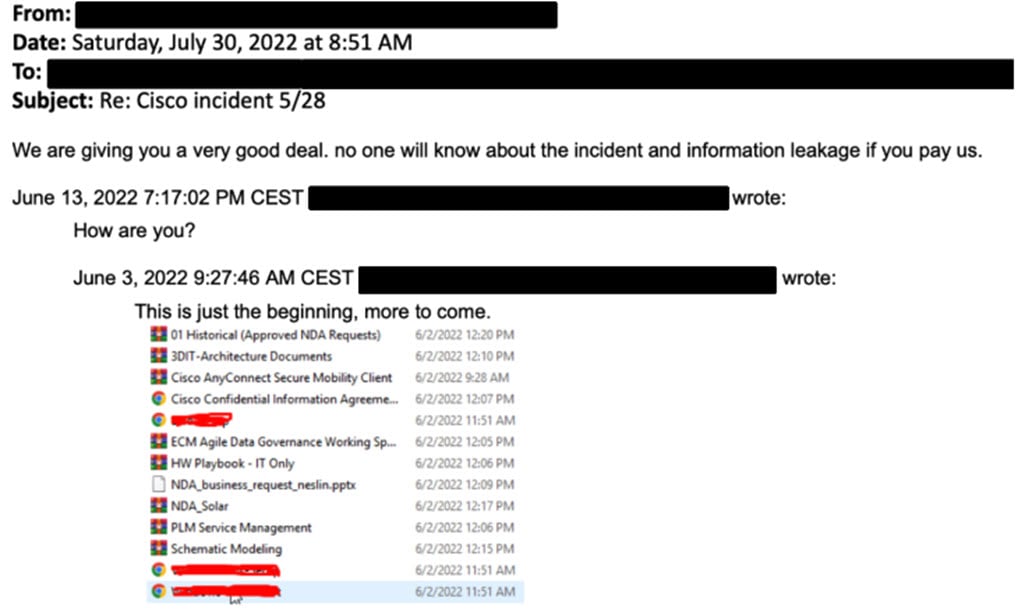
Cisco was able to revoke the attacker’s access, but they tried to gain entry again multiple times using employees’ weak password rotation habits. The attackers also tried getting in touch with Cisco executives, showing off the leaked data and asking Cisco to pay up in order to avoid disclosure.
The gang claiming responsibility for the attack, Yanluowang, has been previously known to target financial institutions but has also targeted manufacturing, IT, consultants and engineering companies. Cisco assessed with moderate to high confidence that the gang has ties to UNC2447 and Lapsus$ and has been previously identified as an initial access broker (IAB).
While there doesn’t appear to be any ransomware deployment in the attack, the TTP used was consistent with “pre-ransomware activity”.
In the News: Whatsapp update allows people to delete messages after 48 hours, leave groups silently and hide status




