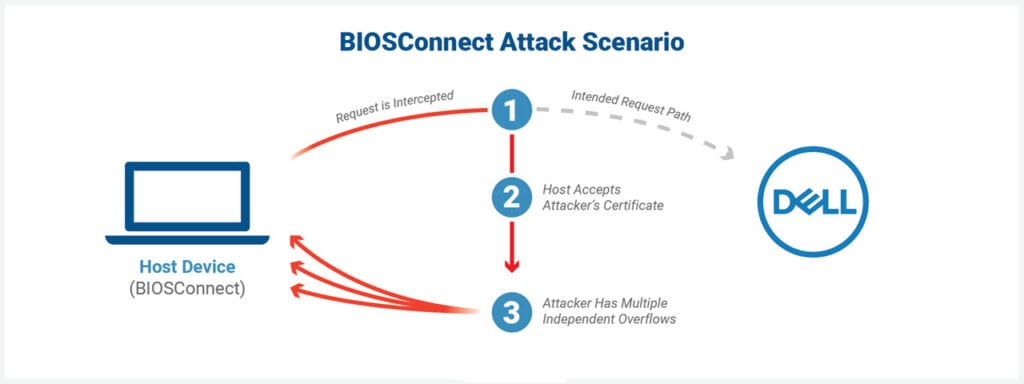
Security researchers have found four major vulnerabilities in Dell’s SupportAssist software, more specifically in the BIOSConnect feature, which allow attackers to execute code within the BIOS remotely.
The SupportAssist software is preinstalled on most Dell PCs running Windows. The BIOSConnect feature allows for remote firmware updates and OS recovery.
Eclypsium discovered the vulnerabilities that come with a cumulative CVSS score of 8.3 let attackers impersonate Dell and run arbitrary code at the BIOS or UEFI level on the impacted devices. The issue affects 129 Dell models and roughly 30 million individual devices.
In the News: Google and Jio collaborate to bring JioPhone Next and accessible 5G
Dell has released security updates
Dell has already provided security updates for the impacted devices and has release remediations for those unable to update their BIOS at the moment. The company released an advisory with a list of affected models and steps on updating the BIOS, alongwith what to do if users can’t.
In a nutshell, users who cannot immediately update their systems are recommended to disable the BiosConnect and HTTPS Boot features from their BIOS setup page or the Dell Command | Configure tool. For others, the company recommends download the latest update and flashing the BIOS from the F12 one-time boot menu.
Vulnerabilities CVE-2021-21573 and CVE-2021-21574 were fixed on the server-side on 28 May 2021, as reported by Dell in its published advisory. Vulnerabilities CVE-2021-21571 and CVE-2021-21572 require updates to the Dell BIOS Client, which have also been released. The company also advised that if the Secure Boot feature is disabled, the potential severity of the CVE-2021-21571 vulnerability may be impacted.
One vulnerability stems from an insecure TLS connection from the BIOS to Dell servers, and the other three are overflow vulnerabilities. According to Eclypsium, “all three vulnerabilities are independent, and each one could lead to arbitrary code execution in BIOS.”
More information on the vulnerabilities can be found in Eclypsium’s report. As of June 24 2021, an update with all vulnerabilities fixed has been pushed by Dell.

In the News: WD My Book Live users find their data deleted overnight




