Departing from previous infection vectors like malspam and compromised YouTube accounts, threat actors now use MetaStealer in malicious ads, denoting a shift in the distribution tactics.
Researchers from Malwarebytes recently analysed the malvertising campaign distributing MetaStealer. The malware’s authors gave an interview hinting at the imminent release of an enhanced version of their malicious tool.
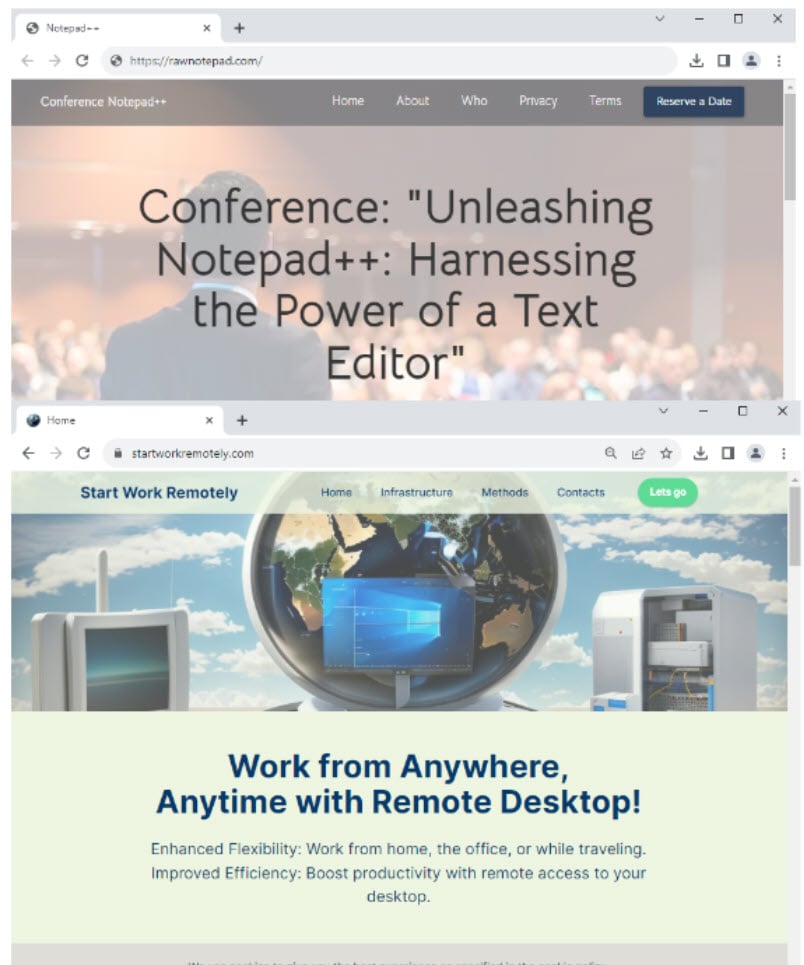
The latest MetaStealer campaign observed by researchers targeted users through deceptive ads for popular software such as Notepad++ and AnyDesk. According to insights from the Google Ads Transparency Center collected by the analysts, the campaigns ran during specific dates in November and December.
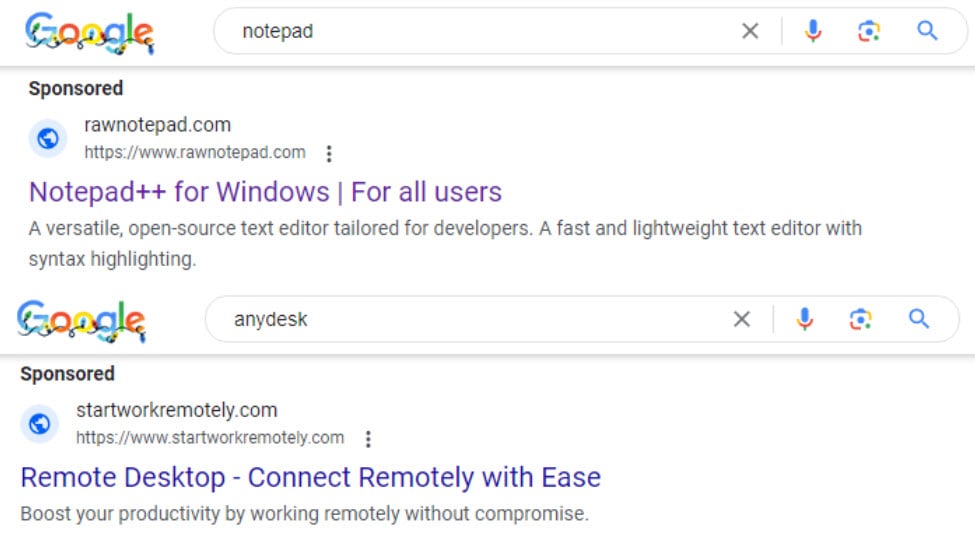
The attacker deployed two domains, presenting them as decoy and landing pages. While the decoy pages appeared generic, those who clicked on the ads and met specific criteria were directed to a malicious landing page with a download link.
The November campaign utilised a payload containing a shortcut launching PowerShell, whereas the December iteration showcased a significant modification. The malware authors removed the PowerShell component and recompiled the malicious DLL.
Despite these changes, network traffic analysis suggests that both payloads belong to the MetaStealer 3.x branch.

The researchers have reported the campaign to Google Ads and got it blocked. MetaStealer gained notoriety in 2022 for leveraging a code from the RedLine malware, becoming a sought-after tool in the criminal underworld where stealers have become highly valuable commodities.
As per the researchers, the malware developers are continuously improving the product. Stealers are highly sought-after products, and the malware authors regularly update them to fulfil the customers’ needs. These can be used by initial access brokers, allowing future ransomware attacks on the system or stealing valuable data such as crypto wallet addresses or login information.
In the News: Novel Terrapin attack allows sequence manipulation on SSH protocol




