Security researchers in the Nautilus team at the Aqua Security firm have found that Travis CI, a service that helps open source developers write and test code, is leaking thousands of authentication tokens and other open source project sequences.
These tokens allow anyone to read or edit code hosted in respective repositories. This ability makes these projects vulnerable to supply chain attacks where an attacker inserts malware in software before its released to the general public. This can be used to target a large number of users in one go by adding malicious code to a project’s production server.
Travis CI’s credential leaking problem has reportedly been an issue since 2015. Back then, the security vulnerability service HackerOne reported that one of its GitHub accounts was compromised because the service exposed an access token for one of HackerOne’s developers. The incident repeated itself in 2019 and then in 2021.
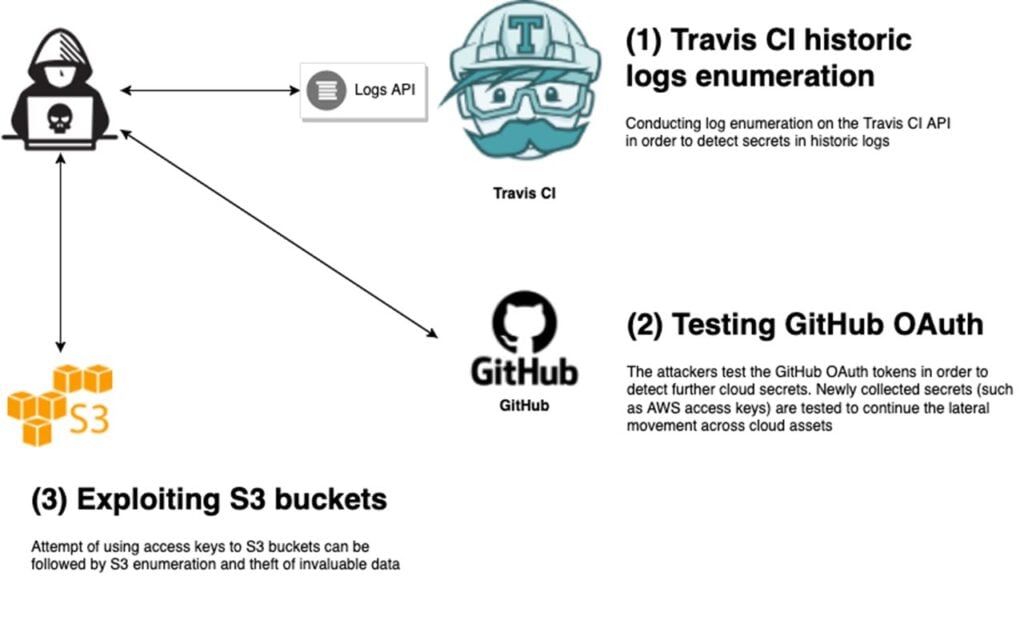
The data found this time around consists of two batches accessed via the Travis CI programming interface consisting of 4.28 million and 770 million logs back from 2013 to May 2022. The researchers further sampled a small amount of data and found 73,000 tokens, secret keys and other credentials. They added that these access keys and credentials were linked to services like AWS, GitHub and Docker Hub.
These GitHub access tokens can allow privileged access to code repositories, and AWS access keys can let threat actors take over services. Leaked credentials can allow access to MySQL or PostgreSQL databases hosted on the internet, and Docker Hub passwords can lead to a complete account takeover if multi-factor authentication isn’t enabled.

Considering how Travis CI has turned a blind eye to these recurring data leaks, it’s best for developers using the service to keep rotating access keys and any other credentials they store with the service. Scanning your code for unknown artefacts or any external snippets can also go a long way in preventing any attacks.
In the News: Google’s Sentient AI, ransomware attacks, Samsung’s next foldable and more




