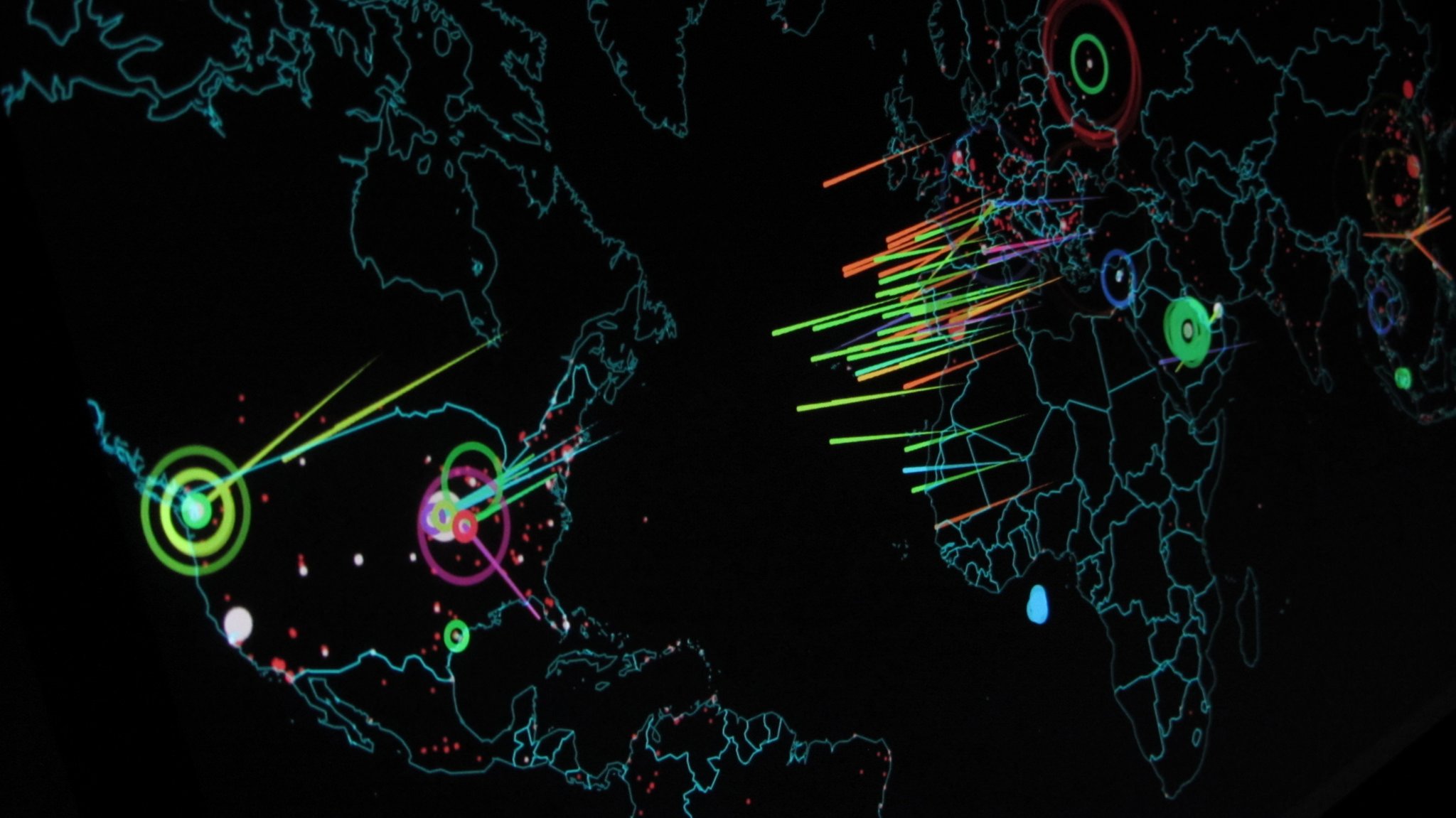
Ever wondered if there were some effective mechanisms using which your organisation is able to detect intrusion and penetration attacks with utmost ease and efficiency? The honeypot counter-attack might be the one for your system.
A honeypot attack is a defence strategy carried out by most organisations to lure and capture any hackers that try to hack into their systems.
Another advantage of this is that the organisation can also get familiarised with any new methodologies the hacker implements while attacking.
This further leads to better understanding of the hacker’s motivation towards attacking the system and accordingly suitable steps can be taken after that to prevent those types of attacks. This often leads to innovation of better methodologies to implement security.
The concept of a honeypot is synonymous to a bear getting attracted to a honey beehive but eventually gets stung by the bees.
The honeypot methodology was first illustrated in Clifford Stoll’s 1989 book The Cuckoo’s Egg. In the book, the author describes his experience of hunting down a hacker who hacked into the Lawrence Berkeley National Laboratory (LBNL).
Using the honeypot ‘sting operation’, Alphabay and Hansa darknet markets were also shut down by the international police in 2017.
Also read: Xiaomi Browser is vulnerable to ‘Man-in-the-Disk’ attack
When two or more honeypots are in a network, it is called a honeynet. Honeypots gained popularity when Lance Spitzner published a paper on honeynets.
“A honey net is a network of high interaction honey pots that simulates a production network and configured such that all activity is monitored, recorded and in a degree, discreetly regulated,” wrote Lance Spitzner.
How is it carried out?
The honeypot is deployed with some false data that replicates legitimate data of the organisation. The honeypot must use low-security measures — have some ports open to allow intrusions that would lead to its detection.
What is important here is the balance by which the security is maintained, i.e., increase the interaction level between your honey pot and the hacker.
Making it is too easy to intrude the system might alarm the hacker, making him a suspect the honeypot trap and you might be unable to trace him after that. A high-level interaction honeypot resembles the actual system and yields better results.
Honeypots can also be used to track any whistleblowers in your organisation. You can deploy the honeypot within your internal system, controlled by a small team.
Surprisingly, the internal system’s honeypot logs show more number of attacks as compared to the external honeypot logs, though a majority of these inadvertent insider threats are due to negligence or accidental.
According to the IBM X-Force Threat Intelligence Index 2018, more than two-thirds of attacks were carried out by insiders.
Honeypots are easy to deploy and maintain and are cost-effective solutions. Even if the attacker is using some encryption techniques to intrude into the system, his activity will still be visible.
Types of Honeypot Attacks
Production honeypots: Helps in finding out in risk in the system and detect any attack on the network.
Research honeypots: Used for discovering new tactics and ways by which the hacker tries to hack into the system and to monitor his methodologies and use this information forward to implement more secure systems.
Shortcomings of using the Honeypot
While the honeypot presents some fantastic solutions to secure systems, it has some shortcomings as well.
If the hacker has access to tools that help detect honeypots, then they can easily bypass the honey pot. If the organisation were entirely relying on the honeypot for its security, then it would be a huge problem.
Also, some privacy issues have recently come in light concerning the use of honeypots and honeynets. Check out this Springer paper that gives better insight on how the privacy of data is a legal concern with the use of the honeypot.
The honeypot must always be monitored in real-time to find any intrusion attacks. The data in the honeypot must look legit but only to a stretch to deter hackers from using the same against your organisation.
Keeping the real balance between making your honeypot as attractive as possible without it being vulnerable is the real challenge of using the honeypot.
You might also like: How to stop Facebook from collecting data via data brokers
https://youtu.be/HvuIYE7UMHs





