Owl Labs’ Meeting Owl Pro is a video conferencing device with several features and several security vulnerabilities that put organisations using the device at risk. A security analysis of the device by security consultancy firm Modzero reveals security flaws that let threat actors access data being sent through the device.
The flaws were discovered when the company performed a security analysis of video conferencing devices for an unnamed client. In January, the firm contacted Owl Labs about these flaws, but none of the most severe vulnerabilities are fixed yet.
In the News: Atlassian Confluence critical 0-day: Company recommends disabling app
Snooping Owl
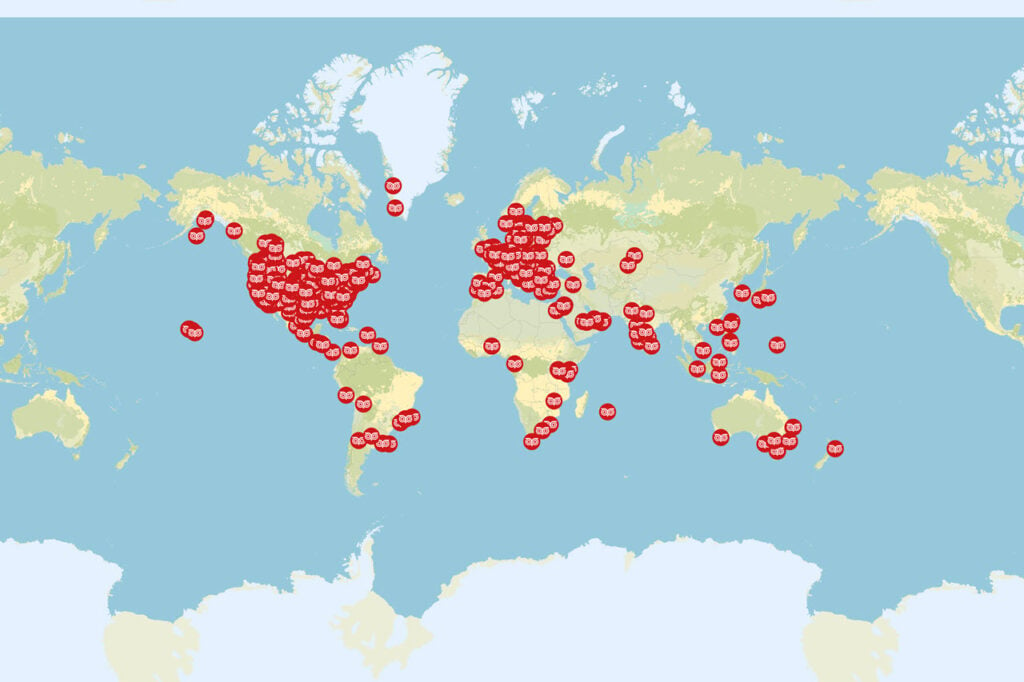
For starters, the names, email addresses, IP addresses and geographic locations of all Meeting Owl Pro users are stored in an online database that can be accessed by just a valid Meeting Owl serial number, with no password required.
There’s a Bluetooth functionality built-in to extend the device’s range and provide remote control, but it doesn’t use a password by default. Even when a passcode is (optionally) set, attackers can disable it using at least four different approaches.
The device can also act as a WiFi extender providing a separate WiFi SSID while using another SSID to stay connected to the organisation’s network. An attacker can exploit this functionality to turn the device into a rogue access point to steal data or insert malware onto the host network.
Last but not least, images of captured whiteboard sessions, something that’s supposed to be available only to meeting participants, can be accessed by anyone. However, in March, Owl Labs disabled this feature after receiving Modzero’s report.
While CVE IDs are still pending, the vulnerabilities have received their severity scores.
| Vulnerability | CVSS Score | CVE ID |
|---|---|---|
| Hardcoded backdoor password | 9.3 | Pending |
| No password is required for Bluetooth commands | 8.2 | Pending |
| Tethering mode uses hardcoded credentials | 7.4 | Pending |
| Passcodes can be deactivated without authentication | 7.4 | Pending |
| Passcode hash can be fetched over Bluetooth | 7.4 | Pending |
Attackers can exploit all these vulnerabilities to find registered devices, the data going through them, and their owners and gain access to the networks these devices are connected to remotely. Attacks can be performed over the internet or by being near the device and can be used to socially engineer or dox employees.
Critical vulnerabilities left exposed since January
Owl Labs did publish a statement acknowledging the vulnerabilities and stated that it either already has or is working on fixing the loopholes pointed out in Modzero’s 41-page security analysis report adding that to the best of its knowledge, there have been no “customer security breaches” yet.
The company further stated that it’s making specific updates to address the following vulnerabilities.
- Personally Identifiable Information would no longer be available from a RESTful API.
- MQTT service restrictions to be implemented to secure IoT communications.
- Previous owners would no longer have access to personally identifiable information when a device is transferred from one account to another.
- Switchboard port exposure access would either be limited or removed altogether.
- Fixes for the WiFi AP tethering mode.
These updates are expected to become available in June 2022.
In the News: DOJ charges former OpenSea exec for insider trading





