Facial recognition technology is a by-product of humans’ insatiable need to get machines to think and act like us. Though it was a relatively early output of this never-ending quest, it is by no means perfect just yet.
There’s something to be said about how science fiction is liberal with its use of face recognition tech, but you rarely see it being employed in real life.
How does facial recognition work? Is it reliable? How easily can it be bypassed? Will it protect your smartphone data well enough? So let’s talk about that.
Also read: Is Tor Browser safe? 8 safety tips for using Tor Browser
How does the Face Recognition tech works?
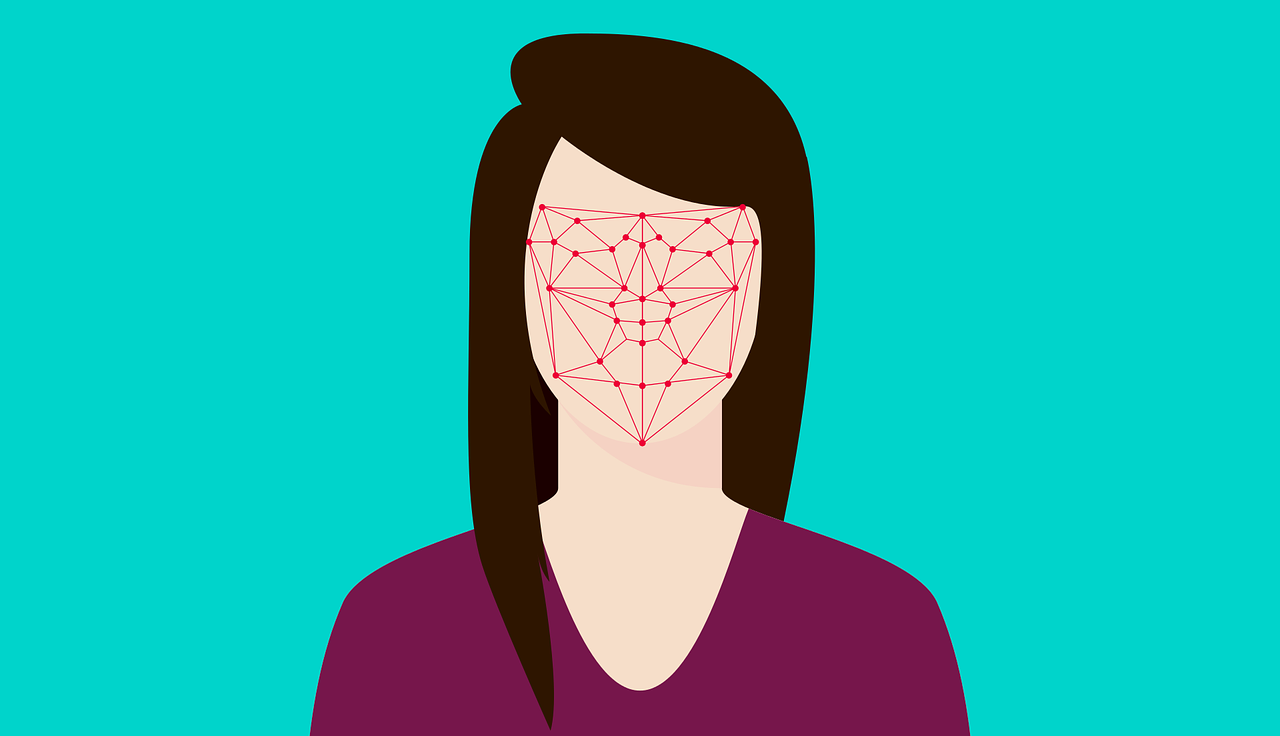
First, the software takes a picture of your face when you try to unlock the phone. Facial recognition software analyses the geometry of your face. Having undergone training with previous models, the software estimates the location of up to 68 specific coordinates on your face.
These coordinates, when mapped, form your facial signature. Your facial signature is essentially a mathematical formula. It is then compared to a database of stored images.
The pictures you provide while setting up face unlocking serve as the database in this case. If the two facial signatures are a close match, the software unlocks your phone.
Advantages of Face Recognition
First and foremost is, of course, the better security provided by biometric data. It also eliminates the hassle of needing to remember passcodes.
Facial recognition can work seamlessly with other software, but it is also the least intrusive method.
It can also have staggeringly high rates of accuracy. Facebook’s face recognition technology has an accuracy rate of 98%
Even low light is not a limiting factor anymore. Newer phones such as the iPhone X use infrared floodlights to illuminate your face even in dim light to capture 3D depth data.
Apple claims that the chances of any random stranger being able to unlock your phone with their face are about 1 in 1,000,000.
Also read: What is Keylogging? 6 ways to protect yourself
Risks of Face Recognition
Every picture of your face that the software captures is stored. It is not too tricky for malicious agents to access and misuse this data.
The surveillance angle is another major player in determining the efficiency of face unlocking. Only a full-frontal image can provide a clear facial signature.
This may not be the most convenient method to unlock your phone, especially when you need to do so secretly.
Besides, the best facial recognition technology comes at steep prices. It is relatively easy to trick cheaper versions of face recognition technology that do not employ depth data.
One can use printed selfies, photos on another screen, or masks to fool the software. A realistic 3D-printed mask fooled even Apple’s advanced FaceID.
Concluding, face unlocking is certainly not without its benefits, but the cons far outweigh the pros here.
Though it is a cool concept on paper, facial recognition had quite a way to go before becoming the standard.
Most notably, the high-risk threats posed to the privacy and security of mobile phone users need to be eliminated. But, unfortunately, until that day, we can but rely on movies to idealise this technology.
Also read: Are free VPNs secure? Should you use them?




